Why it’s a Smart Idea to Use Threat Intelligence
When It Comes to Security, Do You Have ‘Evidence-Based Knowledge’?
Recently, I participated in an interesting Twitter chat. One of the questions posed: What keeps you up at night? The responses varied, but the one common thread was that malware is constantly evolving, making things scarily unpredictable. It’s the reason why intelligence is key to protecting your corporate data and assets, as well as staying one step ahead.
Gartner describes threat intelligence as “the product of a process, rather than a series of individual data points.” Their definition: evidence-based knowledge, including context, mechanisms, indicators, implications and actionable advice, about an existing or emerging menace or hazard to assets that can be used to inform decisions.
It goes on, but suffice it to say they had me at “evidence-based knowledge.” Clearly, intelligence is a critical part of any security posture. According to the SANS Institute, 69 percent of respondents surveyed report implementing threat intelligence to some extent, with only 16 percent saying they have no plans to pursue it in their environments.
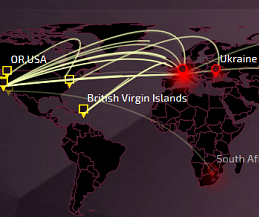
While it’s heartening that the majority are getting the message that it’s needed, those in the 16 percent group are likely to have a tough time of it. Just take a look at the frequency of attacks in this threat map. When you see attacks happening in real time, it elevates the seriousness of the situation. But just like we see in spy movies, intelligence is only as good as its source. At Check Point, our intelligence comes from several feeds that are both internal and external. From there, we analyze the intelligence based on geography, industry and attack types, and then translate that information into specific security protections.
As you evaluate the protections you have in place, make sure you’re looking at data points and network data to provide real-time monitoring, notifications and threat profiles. This is what helps keep you covered and on the path of staying one step ahead.
To learn more about threat intelligence and what we can expect from next-generation malware attacks, join CSO and Check Point on Nov. 18 at CyberDay 2015, an exclusive gathering of some of the top minds in the security industry.









