
The Infamous Nuclear Exploit Kit Shuts Down
In a seeming response to the recent Check Point investigative report, the Nuclear Exploit Kit shut down its entire infrastructure and ceased operation.
Background
The Nuclear Exploit Kit, one of the largest attack infrastructures observed in the wild today, was recently the subject of a thorough investigation conducted by the Check Point Threat Intelligence and Research team as part of our ongoing research into the Malware-as-a-Service industry.
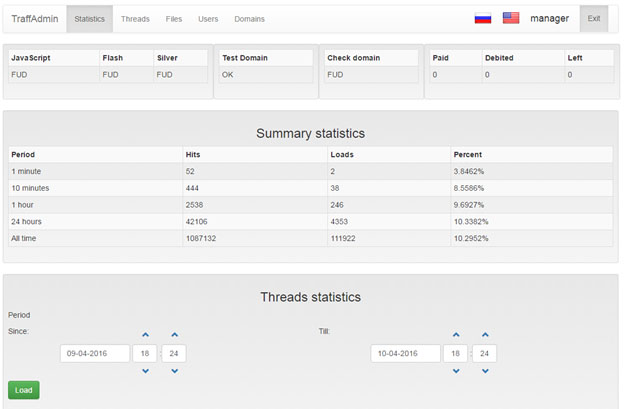
In part I of our report, Inside Nuclear’s Core: Analyzing the Nuclear Exploit Kit Infrastructure, we reviewed in depth the various capabilities, exploits, and techniques employed by the exploit kit. We analyzed Nuclear’s operation scheme and its features, including the control panel, the landing page served by the exploit kit, the master server, infection flow, exploits and other internal logics.
In addition, we presented the active malware campaigns distributed by Nuclear and their infection statistics, and noted that the Locky ransomware was the largest malware campaign distributed via the exploit kit at the time of publication.
Part II of the report, Inside Nuclear’s Core: Unraveling a Malware-as-a-Service Infrastructure, presented a first-of-its-kind view into the heart of a thriving cybercriminal syndicate scene. We reviewed the exploits and vulnerabilities served by the exploit kit and the process of delivering the payload to the victims. We also reviewed the effect of these campaigns on the victims, and assessed the damage caused.
The Aftermath
At the end of April, just a few days after our first report was published, the existing Nuclear infrastructure ceased operation entirely – all Nuclear panel instances and the master server stopped serving malicious content and responding to requests from their IP addresses.
Additional researchers identified that Nuclear has ceased its activities as of late April as well. Kafeine, a French security researcher, reviews in his blog malware.dontneedcoffee.com the current status of the Angler exploit kit, and mentions that Nuclear disappeared around April 30th. In Symantec’s monthly bulletin, Latest Intelligence for May 2016, Symantec refers to the radical change observed in Nuclear’s attack rank in comparison to the previous month – “The Nuclear exploit kit, which topped April’s list, has dropped out of the top five this month, likely due to research that was published in late April, shedding light on the toolkit’s infrastructure and likely leading to disruptions”.
Our investigations and disclosures have clearly had an impact, shutting down a major threat in the wild. Check Point researchers continue to closely monitor changes in Nuclear’s infrastructure and operation.









