
SandBlast Protects Customers from Widespread Cerber Ransomware Attack
Starting at 6:44am UTC on June 22nd, Avanan, a partner of Check Point, detected a large-scale ransomware attack against its Cloud Security Platform customers across multiple companies. We believe this attack was only detected by SandBlast – Check Point’s Zero Day Protection solution. The attack included a very nasty ransomware called Cerber, which spreads through phishing emails and encrypts users’ files with the AES-265 and RSA encryption method. Once encrypted, Cerber demands a ransom of 1.24 bitcoins or ~500 USD be paid in order to regain access of the user’s documents, photos and files.
While it’s difficult to precisely measure how many users were infected, Avanan estimates that 57% of Office 365 email users on its platform experienced the attack, receiving at least one copy of the ransomware in their corporate mailboxes. Based on Avanan’s analysis, while their customers using SandBlast as a backend malware analysis provider were protected from this malware from the first instance, Microsoft only detected the attack roughly 29 hours later and then began blocking the malicious attachment.
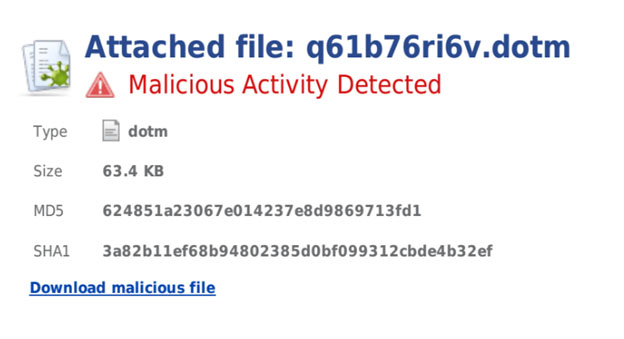
Screenshot of the Cerber ransomware as detected by Check Point SandBlast in the Avanan Cloud Security Platform
“We are continuing to see a significant increase in the complexity of malware targeting business networks and this attack is an excellent example. By utilizing several evasion techniques (and probably testing them in advance against email cloud providers), it was able to bypass other traditional sandboxes. It also speaks to the effort hackers are putting into creating new zero-day attacks and the challenges businesses face in securing their network against cyber criminals,” said Nathan Shuchami, head of threat prevention, Check Point. “Our SandBlast Zero-Day Protection product provides organizations the advanced threat prevention they need to ensure they are effectively secured against the latest threats, with the highest catch rate in the industry.”
“Many users of cloud email programs believe they ‘outsourced’ everything to major cloud email providers such as Microsoft or Google, including security,” explains Gil Friedrich, CEO of Avanan. “The reality is that hackers first make sure their malware bypasses major cloud email providers’ security measures and so most new malware goes through cloud email programs undetected. This is why the majority of the users of Avanan’s Cloud Security Platform activate advanced malware protection layers such as Check Point SandBlast that proved very effective in this incident and many prior incidents in protecting even against the most sophisticated and evasive attacks.”
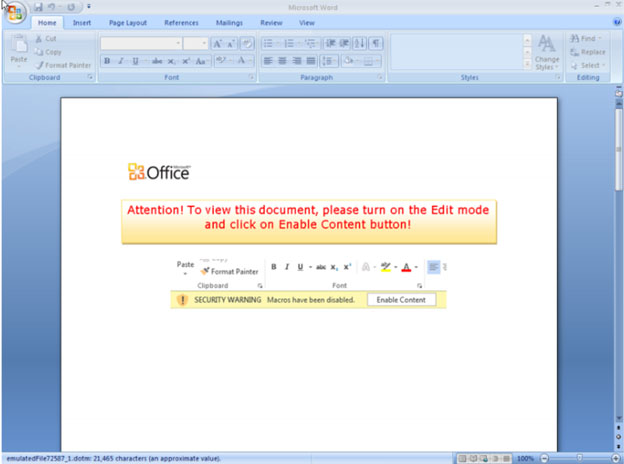
Screenshot of the Cerber ransomware as it appears to infected users
A key takeaway for enterprises from this attack is that not all sandboxing solutions are created equal. When selecting a vendor, whether to protect your enterprise network or cloud applications, you should not only ask about the features of and differences between the products they offer, but should inquire about their malware catch rate.
For more information about Check Point’s SandBlast Zero-Day Protection solutions, click here.









