October’s ‘Most Wanted’ Malware List Shows Attacks on the Rise
Check Point’s Threat Intelligence Research Team revealed today that the number of malware attacks increased in October, as the company released its monthly Global Threat Index, a ranking of the most prevalent malware families attacking organizations’ networks.
The team found that both the number of active malware families and number of attacks increased by 5% during the period, pushing the number of attacks on business networks to near peak levels, as seen earlier this year. Locky ransomware attacks continued to rise, moving it up from third to second place, while the Zeus banking trojan moved up two spots, returning it to the top three. The reason for Locky’s continued growth is the constant variation and expansion of its distribution mechanism, which is primarily through spams emails. Its creators are continually changing the type of files used for downloading the ransomware, including doc, xls and wsf files, as well as making significant structural changes to the spam emails. The actual ransomware itself is nothing exceptional, but cyber criminals are investing a lot of time into maximizing the number of machines that become infected by it. For the seventh consecutive month, HummingBad, an android malware that establishes a persistent rootkit to carry out an array of malicious purposes, remained the most common malware used to attack mobile devices.
Once again Conficker retained its first place position as the world’s most prevalent malware, responsible for 17% of recognized attacks. Both second placed Locky, which only started its distribution in February of this year, and third placed Zeus, were responsible for 5% of known attacks.
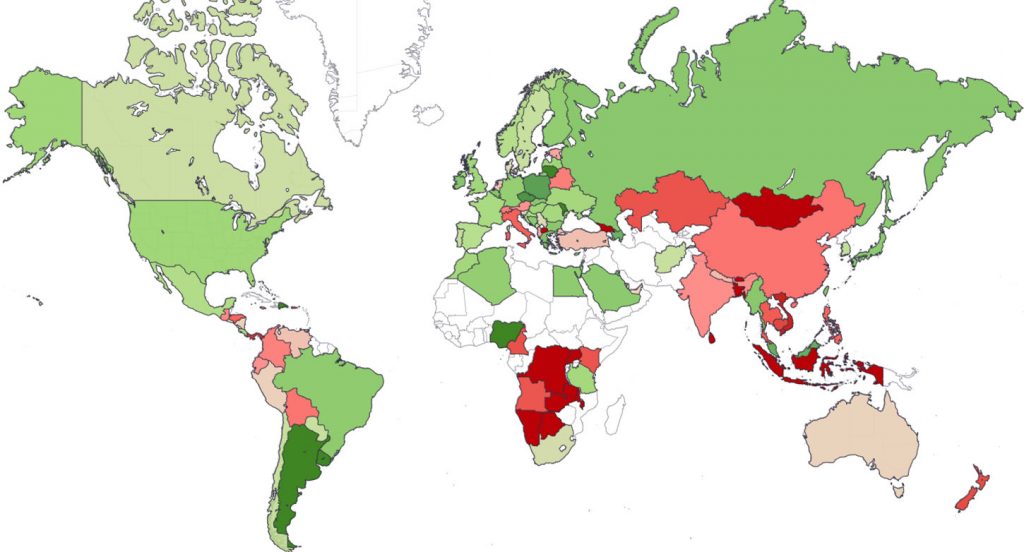
October 2016 World Cyber Threat Map – click image to view the live interactive map
The map displays the risk index globally. Green = Low Risk Beige = Medium Risk Pink = Higher Risk Red = High Risk White = Insufficient Data
October’s Top 10 ‘Most Wanted’ Malware
- ↔ Conficker – Worm that allows remote operations and malware download. The infected machine is controlled by a botnet, which contacts its Command & Control server to receive instructions.
- ↑ Locky – Ransomware that started its distribution in February 2016, and spreads mainly via spam emails containing a downloader disguised as a Word or Zip file attachment, which then downloads and installs the malware that encrypts the user files.
- ↑ Zeus – Trojan that targets Windows platforms and often used to steal banking information by man-in-the-browser keystroke logging and form grabbing.
- ↔ Cutwail – Botnet mostly involved in sending spam e-mails, as well as some DDoS attacks. Once installed, the bots connect directly to the command and control server, and receive instructions about the emails they should send. After they are done with their task, the bots report back to the spammer exact statistics regarding their operation.
- ↓ Sality – Virus that allows remote operations and downloads of additional malware to infected systems by its operator. Its main goal is to persist in a system and provide means for remote control and installing further malware.
- ↑ Tinba – Banking Trojan that steals the victim’s credentials using web-injects and is activated when the users try to login to their bank’s website.
- ↑ HackerDefender – User-mode Rootkit for Windows that can be used to hide files, processes and registry keys, and also implements a backdoor and port redirector that operates through TCP ports opened by existing services. As a result, it is not possible to find the hidden backdoor through traditional means.
- ↔ Cryptowall – Ransomware that started as a Cryptolocker doppelgänger, but eventually surpassed it. After the takedown of Cryptolocker, Cryptowall became one of the most prominent ransomware to date. Cryptowall is known for its use of AES encryption and for conducting its Command & Control communications over the Tor anonymous network. It is widely distributed via exploit kits, malvertising and phishing
- ↑ Parite – Virus that infects executable files (.exe and .scr) on the infected host and network drive. It drops a malicious DLL file into the Windows temporary directory, which is injected into the explorer.exe process when an infected file is executed.
- ↑ Virut – Botnet that is known to be used for cybercrime activities such as DDoS attacks, spam, fraud, data theft and pay-per-install activities. It spreads through executable file infection (through infected USB sticks and other media), and more recently, through compromised HTML files (thus infecting vulnerable browsers visiting compromised websites).
October’s Top 3 ‘Most Wanted’ Mobile Malware
Mobile malware families continued to pose a significant threat to businesses, with 15 of the top 200 malware families targeting mobile devices. The three most common mobile families were:
- ↔ HummingBad – Android malware that establishes a persistent rootkit on the device, installs fraudulent applications and enables additional malicious activity such as installing a key-logger, stealing credentials and bypassing encrypted email containers used by enterprises.
- ↔ Triada – Modular Backdoor for Android that grants super-user privileges to downloaded malware, as helps it to get embedded into system processes. Triada has also been seen spoofing URLs loaded in the browser.
- ↑ XcodeGhost – A compromised version of the iOS developer platform, Xcode. This unofficial version of Xcode was altered so that it injects malicious code into any app that was developed and compiled using it. The injected code sends app information to a Command & Control server, allowing the infected app to read the device clipboard.
Nathan Shuchami, Head of Threat Prevention at Check Point explained, “With the number of attacks and malware families increasing, the scale of the challenge organizations face in ensuring their networks remain secure is tremendous. The fact the top ten malware remained virtually the same as September suggests that cyber criminals have enjoyed a considerable amount of success with these attack methods, signaling to organizations that they need to proactively respond to protect their critical business assets. It is particularly concerning that a malware family as established and well known as Conficker is so effective, suggesting that organizations aren’t using the latest, multi-layered defenses.”
About the Check Point Threat Index
Check Point’s Threat Index is based on threat intelligence drawn from its ThreatCloud World Cyber Threat Map, which tracks how and where cyberattacks are taking place worldwide in real time. The Threat Map is powered by Check Point’s ThreatCloudTM intelligence, the largest collaborative network to fight cybercrime, which delivers threat data and attack trends from a global network of threat sensors. The ThreatCloud database holds over 250 million addresses analyzed for bot discovery, over 11 million malware signatures and over 5.5 million infected websites, and identifies millions of malware types daily.