JAFF – A New Ransomware is in town, and it’s widely spread by the infamous Necurs Botnet
Necurs, one of the largest botnets, went offline during the holiday period of 2016 and through the beginning of 2017. However it returned only to shortly peak late in April, spreading Locky using malicious PDF documents.
Today, May 11, Necurs started spreading a new ransomware called JAFF.
Check Point’s global sensors have spotted as many as 40,000 emails in the last few hours, at an infection rate of approximately 10,000 emails sent per hour.
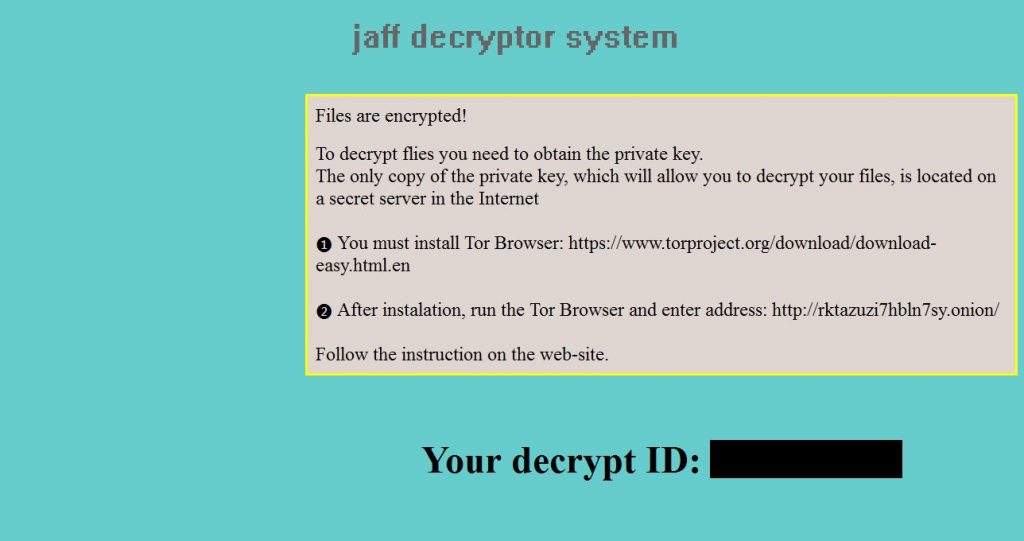
Image 1: The JAFF ransomware ransom note (courtesy of MalwareHunterTeam)
Necurs has the reputation for being one of the ‘best’ malware distributors. In the past, it helped Locky and Dridex reach millions of victims, making them ‘legends’ in the ransomware and bankers landscapes respectively. We thus suspect that JAFF might quickly climb to our list of top malware.
In the current JAFF ransomware campaign, Necurs is sent via spam emails containing a PDF attachment.
The PDF file contains an embedded DOCM file which, when opened, prompts the user to allow opening the DOCM file. The DOCM then runs a macro which downloads an encrypted TXT file, which is then decrypted by the macros in the doc, and turns into a malicious EXE file which will execute the JAFF ransomware.
Image 2: The Necurs>JAFF infection chain
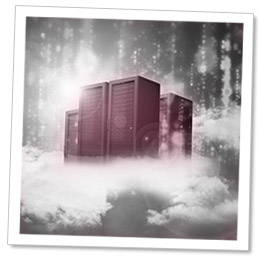
Image 3: The JAFF ransomware decryptor page (courtesy of MalwareHunterTeam)
The campaign makes a large reuse of files; the exact same malicious files were spotted at hundreds of different users’ email boxes.
The currently requested ransom amount is 2.047 BTC (approximately $3,800 as of today).
Check Point customers are protected from JAFF by our SandBlast Zero-Day Protection.