Threat Emulation Identifies Spear Phishing Attack Using Near-Zero-Day Malware
Summary
On October 22, 2013, Check Point’s ThreatCloud Threat Emulation service analyzed suspicious documents sent by email to end users at a media company. Analysis of the malware, which was intercepted through a Message Transport Agent (MTA) configuration and sent to the Threat Emulation Service for sandboxing, revealed that the documents exploited a vulnerability in Microsoft Word in order to install a seldom-detected variant of the Zeus/ZBOT Trojan.
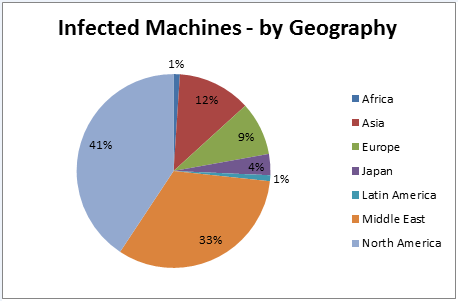
Over the following days, Check Point’s ThreatCloud Emulation Service detected a similar attack on four additional organizations in UK, Italy, Turkey and Greece. Further investigation by Check Point security researchers determined that the phishing emails which distributed this malicious document part of a larger campaign targeting specific organizations around the world, with a focus on communications, transportation finance, and finance-related government agencies.
Detailed Analysis
Interception of malicious documents in a phishing attack
On October 22nd, a media company received six suspicious emails which were subsequently analyzed by Check Point ThreatCloud Emulation Service.
-
From: No-Replay@UPS.COM
-
Subject: UPS Delivery Notification
-
Attachment: invoiceBQW8OY.doc (MD5 ad0ef249b1524f4293e6c76a9d2ac10d)
This organization is using the Check Point ThreatCloud Emulation Service, and all suspicious incoming documents are sent to the Emulation Service for analysis. Threat Emulation allows organizations to detect and prevent malicious attachments from arriving to their destinations when using an MTA (Message Transport Agent) configuration.
During the emulation process – which involves simulation in a virtual sandbox of a user opening a potentially malicious file – an abnormal behavior was detected
- Microsoft Word crashed and reloaded with an empty document
- A registry key was set – HKCUSoftwarebbbedafsacfsfdsfCurrentPath111
- A new process was initiated on the end device C:ProgramDatabbbedafsacfsfdsf.exe
As a result, Check Point Threat Emulation Service determined that this file is malicious.
Analysis of the malicious document
Further analysis by Check Point security researchers discovered that the documents from all six emails were identical and exploited the CVE-2012-0158 vulnerability, affecting Microsoft Word. This vulnerability is also known as the MSCOMCTL.OCX RCE, and allows remote code execution on the end-device. All base versions of Microsoft Office 2003-2010 are vulnerable to this exploit.
Check Point security research analyzed the malicious payload – which was identified as a customized variant of the ZBOT Trojan – that steals information by man-in-the-browser attacks, keystroke logging, form grabbing, and other methods.
Observing these samples at VirusTotal reveals a low (<10%) detection rate for both the malicious attachment and the ZBOT variant at the time of submission.
- Two out of 46 available antivirus vendors were capable of detecting this malicious attachment
- Three out of 46 detected this custom ZBOT variant. The MD5 hash of the executable payload from the exploit is 62e25cc76291a3f348324172ff306ba0.
Further analysis of the malicious campaign
Check Point security researchers analyzed the different URLs from which the malicious document was downloaded, uncovering a list of unique parameters passed to the infecting servers. They also discovered that these parameters were, in fact, a base64 encoded target designator, containing the targeted e-mail address. These unique URLs represented email addresses of users in large international organizations that were targeted by this attack.
Among those organizations we identified global organizations and corporations such as financial institutions, international car manufacturers, telcos, government agencies and North American education and municipal organizations. These targets suggest that these attacks are part of a targeted campaign designed to capture user credentials, banking information, and other information that could be used to gain access to the targeted organizations’ most sensitive data.
Protecting your organization from this type of attack
All Organizations
- Ensure that end-user systems running Microsoft Office have the latest patches available from Microsoft. This attack exploits a known vulnerability of Microsoft Office versions 2003-2010.
- Educate users not to open unexpected or suspicious attachments from external email addresses. This attack is driven by a spear-phishing email appearing to arrive from UPS (e.g., the sender email address was no-replay@UPS.com).
Check Point Customers
Customers who have enabled the Antivirus Blade on their Check Point gateways automatically receive updated detections for these newly detected variants through ThreatCloud. For additional protection against previously undetected variants, customers should consider enabling the ThreatCloud Emulation Service.
Non-Check Point Customers
Non-Check Point Customers should monitor their email server and email gateway logs for emails from this address, and consider adding blocking at their gateway for this email source.
Appendix
The following variants of email attachments, MD5 and processes were detected:
Attachment Name: invoiceCM0V9ORWJF23KX8PAP.doc
MD5: b20d0254faedc6608d640290aeb20b4a
Loaded Process: C:Documents and SettingsAll UsersApplication Datadebedeafdfddbsacfsfdsf.exe
Attachment Name: invoiceCM0V9ORWJF23KX8PAP.doc
MD5: b20d0254f aedc6608d640290aeb20b4a
Loaded Process: C:ProgramDatabbbedafsacfsfdsf.exe
Attachment Name: invoiceU6GCMXGLL2O0N7QYDZ.doc
MD5: 7c2fd4abfe8640f8db0d18dbecaf8bb4
Loaded Process: C:Documents and SettingsAll UsersApplication Datadebedeafdfddbsacfsfdsf.exe
Attachment Name: invoiceBQW8OYJDDGXIPN8H63.doc
MD5:d0ef249b1524f4293e6c76a9d2ac10d
Loaded Process: C:ProgramDatabbbedafsacfsfdsf.exe
Resources
Submit a suspicious file for Threat Emulation: https://threatemulation.checkpoint.com/teb/upload.jsp