
New OpenSea attack led to theft of millions of dollars in NFTs
By Dikla Barda, Roman Zaikin & Oded Vanunu
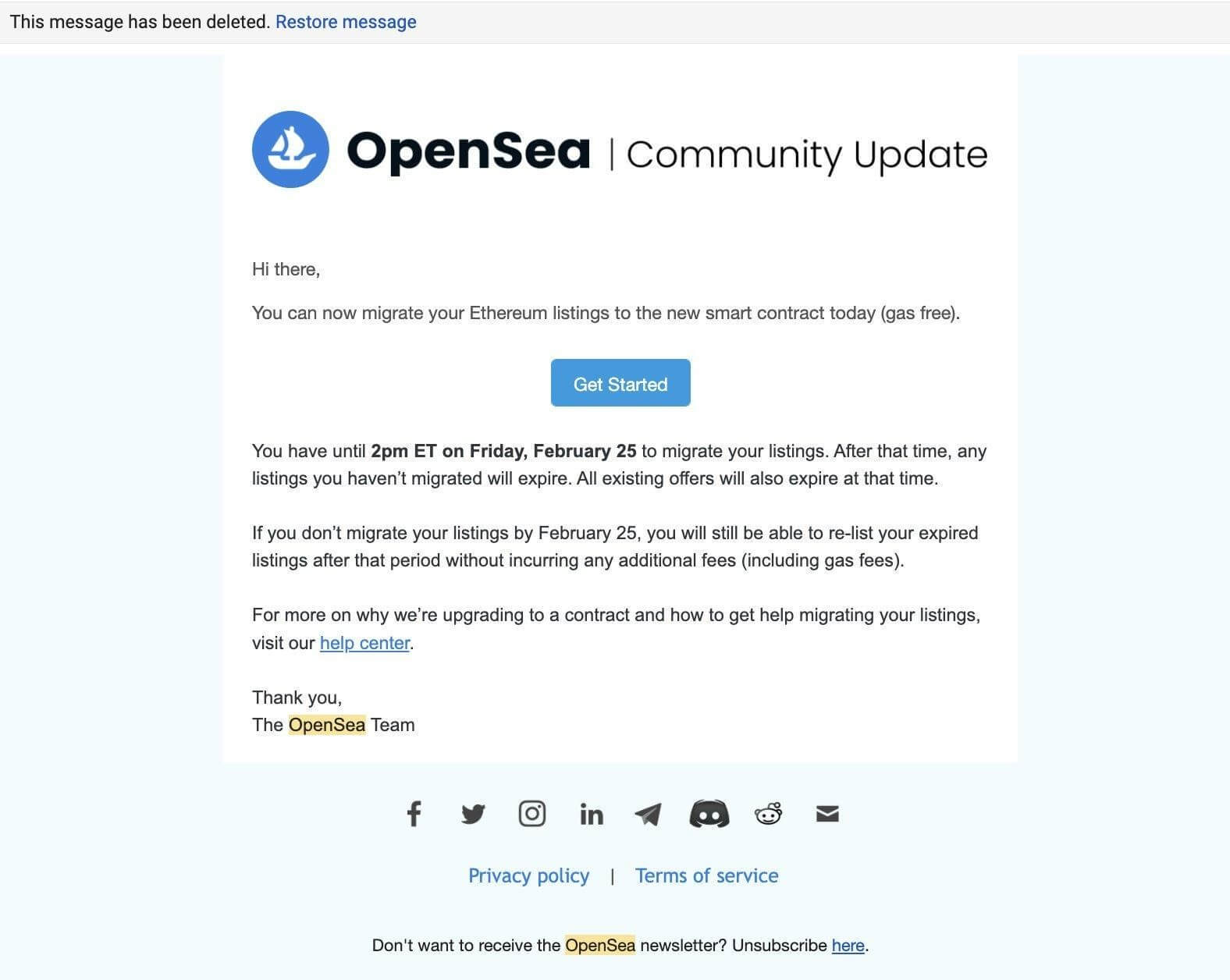
A few days ago, OpenSea published an article about the contract migration they are planning.

The idea behind the OpenSea migration is to address the existing inactive listings of old NFT’s, and in order to do that, they are planning to upgrade to a new contract. All users will be required to “migrate” their listings on Ethereum to the new smart contract.
They also sent instructions, which can be found here:
Following public information that was published in the social media and users alerts we started the investigation and we believe that hackers took advantage of the upgrade process and decided to scam NFT users by using the same email format from OpenSea and resending it to the OpenSea victims:
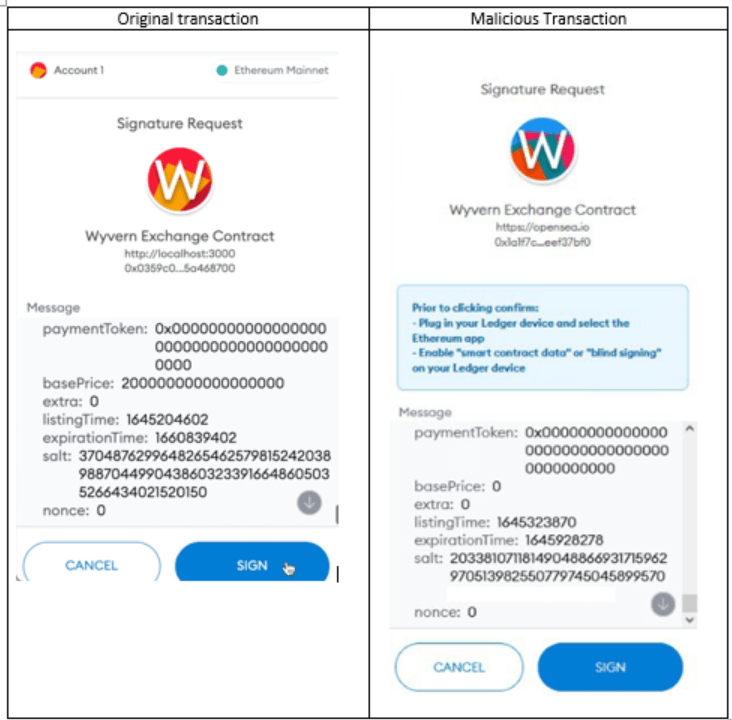
Pressing on the link would navigate the users to a phishing website which would ask the users to sign a transaction that looks like the transaction from the OpenSea blog:
https://twitter.com/isotile/status/1495234649970421760?s=21
[**Update*** 23/2/22 – to mitigate the phishing attack users must follow OpenSea recommendations explicitly via Twitter**]
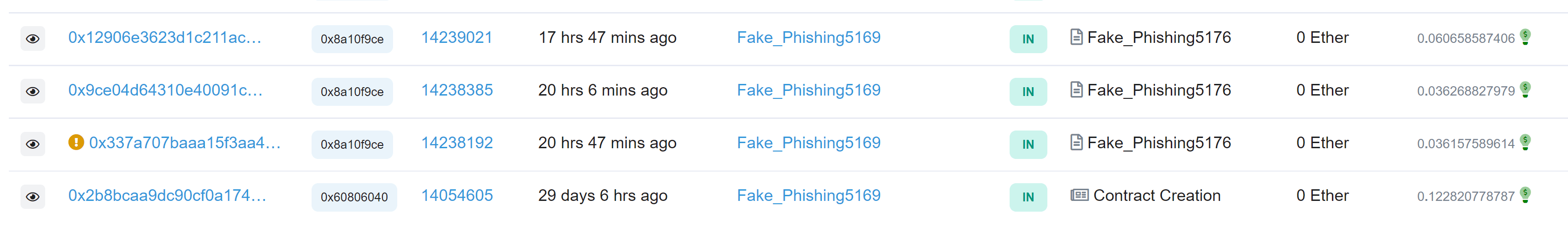
By signing the transaction, an atomicMatch_ request would be sent to the attacker contract, which he created a month ago prior to the attack. (https://etherscan.io/address/0xa2c0946ad444dccf990394c5cbe019a858a945bd):
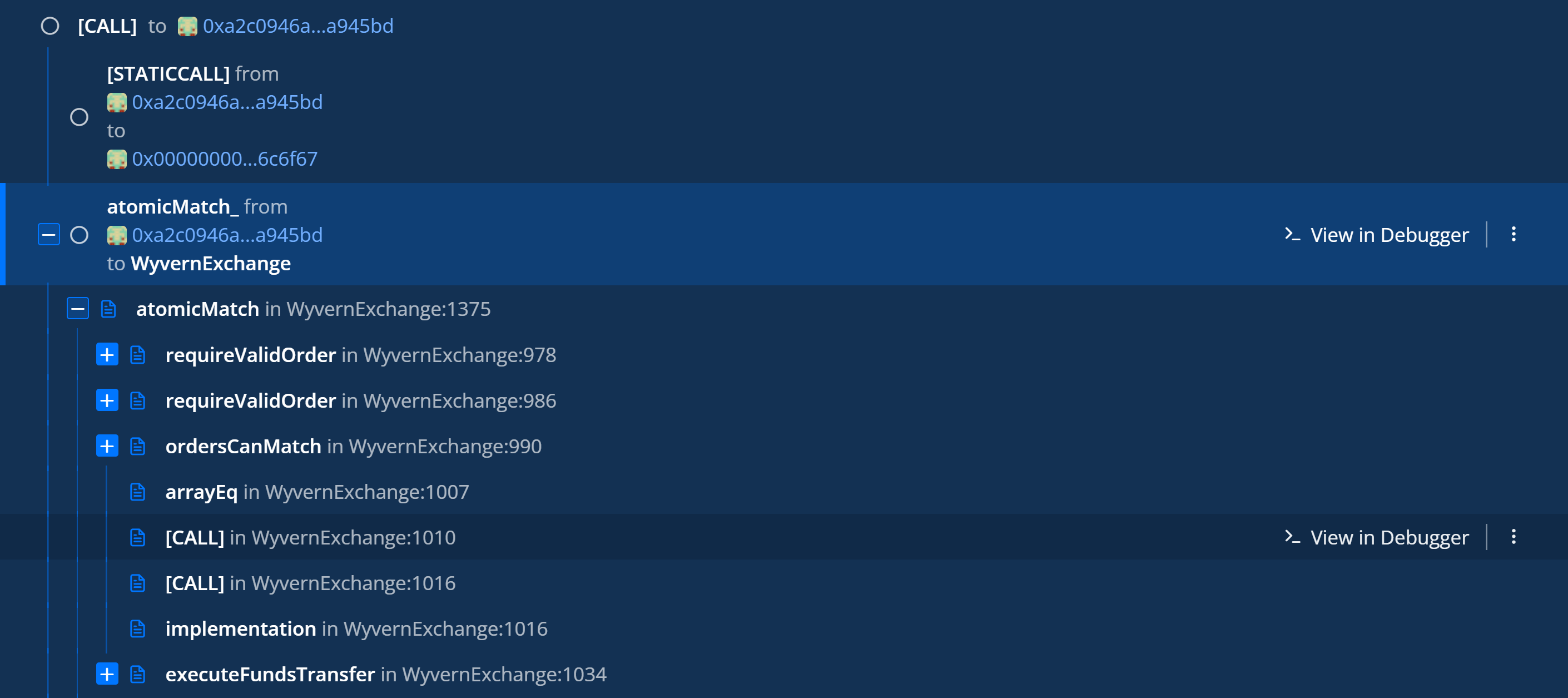
From there, the atomicMatch_ would be forwarded to the Project Wyvern Exchange. atomicMath is responsible for all the Trading on OpenSea with minimal trust. Atomic means that the transaction will only take place if all the parameters of the transaction are met. And this is how all the NFTs are moving around accounts at OpenSea.
This is why the attacker decided to use the atomicMatch to steal the victim NFTS because this kind of request is capable of stealing all victim NFTS in one transaction.
The flow of the attack looks as follows:
- Victim clicks on a malicious link from the phishing email
- The link opens a phishing website and asks the victim to sign a transaction.
- By signing the transaction an atomicMatch_ request would be sent to 0xa2c0946ad444dccf990394c5cbe019a858a945bd (attacker contract).
- Attacker than forward the request to atomicMath at 0x7be8076f4ea4a4ad08075c2508e481d6c946d12b (OpenSea contract)
- OpenSea Contract verifies all the parameters of the deal and executes the transaction because everything is signed by the victim and approved.
- OpenSea contract communicate with the NFT contracts and transfer the NFT from the victim to the attacker according to the atomicMatch
The whole process looks like that:
What is even more interesting here is that the attacker executes a dry run before the attack. He tries to execute an atomicMatch to OpenSea and verifies his attack.
As can be seen in the following screenshot:
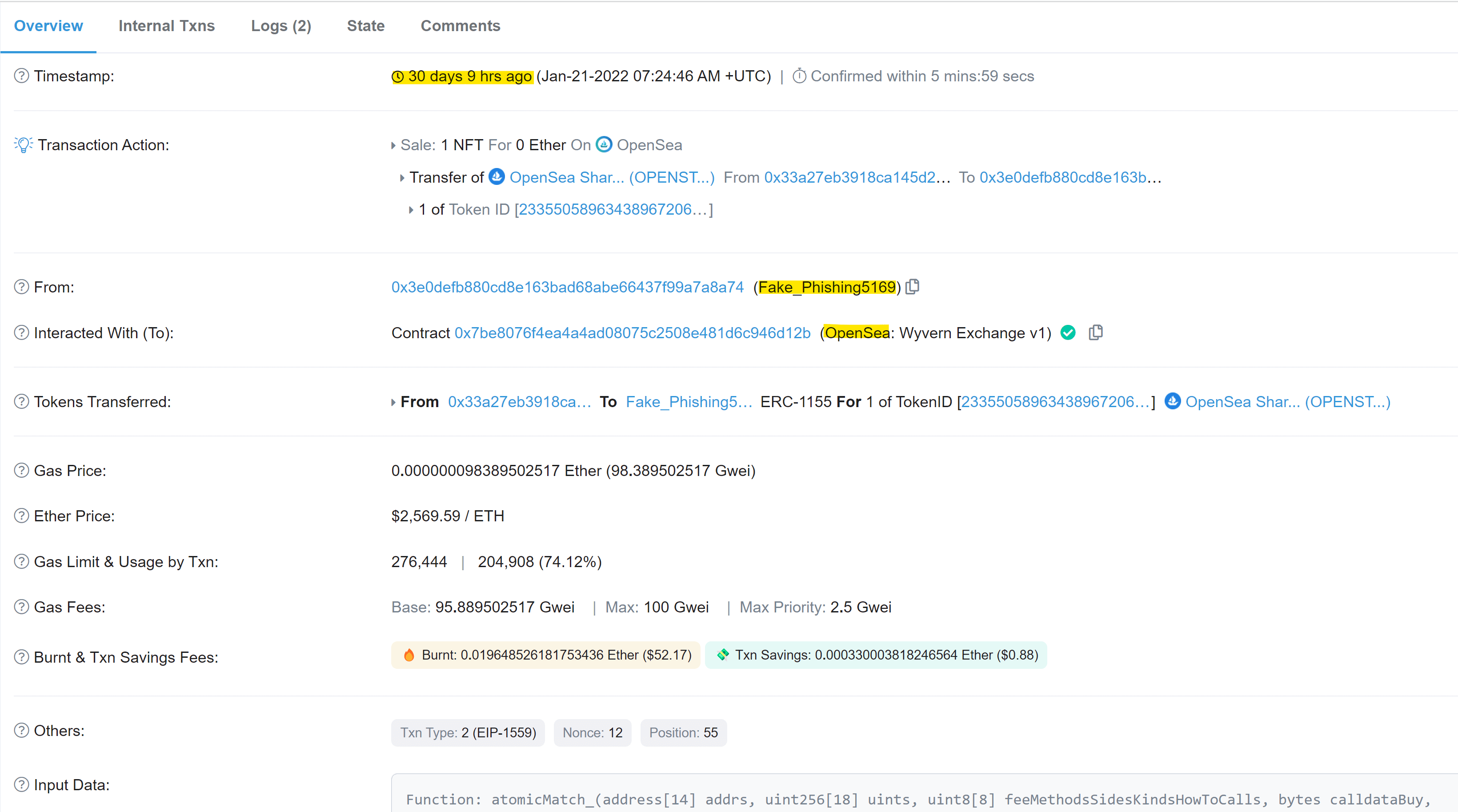
From the transactions in the attacker account, Check Point Research can see that the wallet has over 2 million dollars worth of Ethereum from selling some of the stolen NFTs.
https://etherscan.io/address/0x3e0defb880cd8e163bad68abe66437f99a7a8a74#internaltx
How to stay safe?
- Many websites and projects request a permanent access to your NFT’s by sending you a transaction to sign. This transaction will give the websites/projects access anytime they want to your NFT unless you un-approve the transaction at the following link – https://etherscan.io/tokenapprovalchecker.
- Signing a transaction is similar to giving someone permission to access all your NFT’s and cryptocurrencies. This is why signing is very dangerous. Pay extra attention to where and when you sign a transaction.
- Phishing emails may be tricky. We don’t recommend clicking on links from emails no matter who is the sender, always try to find the same information on the website provider.









