

Avanan now enhances protection against phishing attacks that abuse Microsoft 365 calendar invitations by ensuring malicious calendar events are removed even when the original email is blocked.
Phishing attacks continue to evolve, and attackers increasingly use malicious calendar invitations to trick users into interacting with fraudulent meetings, links, or attachments. While Avanan’s inline protection already prevents these attacks from reaching users’ inboxes, calendar-based artifacts can sometimes remain in the user’s calendar even after the original email is blocked.
With this enhancement, Avanan automatically removes malicious calendar invitations when the associated phishing email is blocked. This ensures that users are not exposed to lingering calendar events that could still lead them to malicious links or social engineering attempts. By extending protection beyond the inbox and into the calendar environment, organizations gain stronger end-to-end defense against phishing campaigns that attempt to exploit collaboration tools.
In order to support this capability, Avanan requires permission to remove calendar invitations through the Microsoft 365 Mail application. Customers who deployed Avanan prior to March 2026 should re-authorize the Office 365 Mail app to grant the required permission.
To re-authorize the application:
Go to Security Settings > SaaS Applications
Select Office 365 Mail
Click Configure
Click “Re-Authorize Check Point Office365 Emails App”
Approve the requested permissions
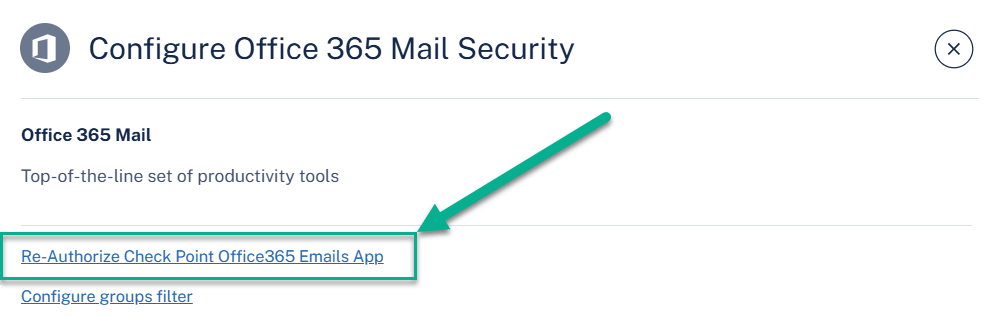
Note – The permissions must be approved using a Microsoft 365 account from the protected tenant with at least the Privileged Role Administrator role.