
Global Cyber Attacks Remain Near Record Highs in February 2026 Despite Ransomware Decline
Global Attack Volumes Remain Elevated Worldwide
In February 2026, global cyber attack activity remained near record levels, confirming that elevated attack volumes are becoming the new normal for organizations worldwide. The average number of weekly cyber attacks per organization reached 2,086, representing a 9.6% increase year over year, while remaining essentially flat month over month (-0.2% compared to January 2026). This stabilization at a high baseline reflects a sustained pressure environment rather than a short‑term surge. Despite a slowdown in ransomware activity compared to the same period last year, overall attack volumes continue to rise, driven by automation, expanding digital footprints, and persistent exposure risks linked to enterprise GenAI usage. Check Point Research data shows that February’s figures reinforce a broader trend: cyber threats are not episodic but continuous, with attackers maintaining steady operational tempo across regions and industries.
Critical Sectors Remain Under Heavy Pressure
The education sector continued to be the most targeted industry in February, facing an average of 4,749 cyber attacks per organization per week, a 7% increase year over year. Large user populations, open access environments, and limited security resources continue to make education institutions highly attractive to threat actors. The government sector ranked second, with organizations experiencing 2,714 weekly attacks on average, reflecting a 2% year‑over‑year increase. While growth was more moderate, government entities remain a consistent target due to their mission‑critical services and high‑value data.
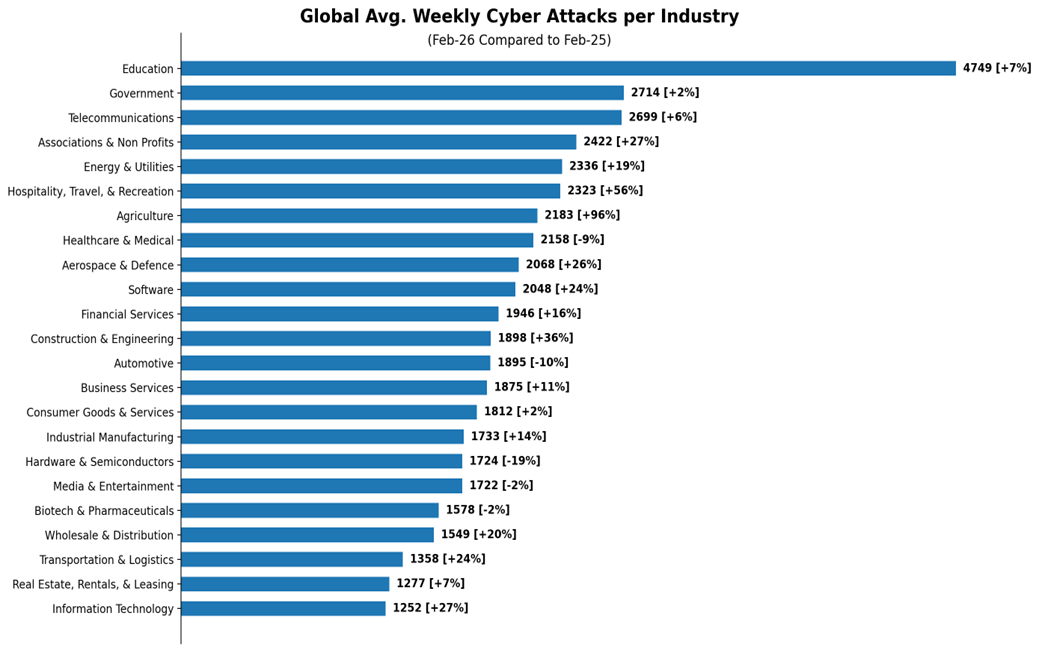
Telecommunications remained the third most targeted sector, averaging 2,699 weekly attacks per organization, up 6% year over year. As reliance on digital connectivity, 5G infrastructure, and cloud‑based services continues to grow, telecom providers remain central targets for attackers seeking large‑scale disruption or access through supply‑chain dependencies.
Regional Threat Disparities Persist
A regional breakdown highlights continued imbalance in global cyber attack activity, with emerging and rapidly digitizing regions bearing the highest burden. Latin America recorded the highest average number of attacks worldwide, with 3,123 weekly attacks per organization, alongside the largest year‑over‑year increase (+20%). This sustained growth underscores the increasing focus on fast‑growing digital economies.
APAC followed closely, reporting 3,040 weekly attacks per organization, a 3% increase year over year, while Africa averaged 2,993 weekly attacks, reflecting a-7% decline year over year, though remaining among the most targeted regions globally.
| Region | Weekly Attacks per Organization | YoY Change |
| Latin America | 3,123 | +20% |
| APAC | 3,040 | +3% |
| Africa | 2,993 | -7% |
| Europe | 1,764 | +11% |
| North America | 1,456 | +9% |
Europe and North America both experienced notable increases compared to February 2025, with +11% and +9% growth respectively, reinforcing that mature markets continue to face rising cyber pressure. This distribution highlights a globally entrenched threat environment, with no region immune to sustained cyber pressure.
GenAI Adoption Continues to Drive Data Exposure Risk
Enterprise GenAI usage remained widespread in February 2026, continuing to introduce significant data leakage risk across organizations.
February highlights include:
- 1 in every 31 GenAI prompts posed a high risk of sensitive data leakage
- 88% of organizations using GenAI tools regularly were impacted by this risk
- Additional 16% of prompts contained potentially sensitive information
- Organizations used an average of 11 different GenAI tools, indicating fragmented adoption
- The average enterprise user generated 62 GenAI prompts per month
Although overall prompt volumes declined slightly compared to January, the persistence of high‑risk interactions points to ongoing governance and visibility gaps. Without centralized controls and consistent policies, organizations remain exposed to credential leaks, proprietary data disclosure, internal document mis‑sharing, and unintended supply‑chain exposure.
Ransomware Activity Rebalances After 2025 Spike
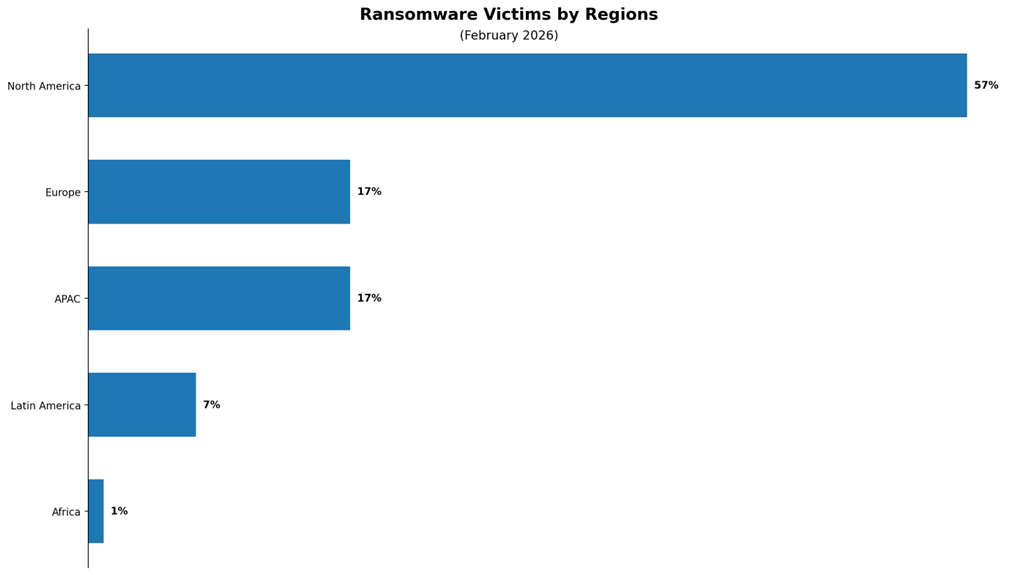
In February 2026, 629 ransomware attacks were reported globally, reflecting a 32% decrease year over year. This decline is primarily attributed to an unusually large ransomware campaign conducted by the Clop group during the same period in 2025. Excluding that anomalous event, ransomware activity remains broadly consistent year over year, reinforcing ransomware’s position as a persistent and structurally embedded threat. North America accounted for 57% of reported ransomware incidents, followed by Europe (17%) and APAC (17%), showing attackers’ continued focus on regions with dense digital infrastructure and high monetization potential.
(*) This data draws from ransomware “shame sites” operated by double‑extortion groups. While these sources contain inherent biases, they provide valuable insight into ransomware activity and trends.
Ransomware Targets Concentrate on High‑Impact Industries
Business services was the most targeted sector, accounting for 37% of ransomware victims, followed by consumer goods & services (13%) and industrial manufacturing (9%). Together, the top three industries represented 59% of reported incidents, illustrating attackers’ focus on sectors where downtime and data exposure translate directly into financial and reputational damage.
| Industry | Ransomware Victims |
| Business Services | 37% |
| Consumer Goods & Services | 13% |
| Industrial Manufacturing | 9% |
| Financial Services | 5.1% |
| Information Technology | 4.8% |
| Healthcare & Medical | 4.3% |
| Transportation & Logistics | 4.0% |
| Automotive | 4.0% |
| Government | 4.0% |
| Real Estate, Rentals, & Leasing | 3.0% |
| Education | 2.4% |
| Media & Entertainment | 1.9% |
| Hospitality, Travel, & Recreation | 1.8% |
| Critical Infrastructures | 1.1% |
| Telecommunications | 0.9% |
| Energy & Utilities | 0.9% |
| Chemicals and Allied Products | 0.8% |
Ransomware Attacks per Country
Country‑level analysis highlights a strong concentration of ransomware activity, particularly in North America, while still reflecting broad global reach. The United States was the most impacted country, accounting for 51% of all reported ransomware attacks. Canada followed with 6%, while the United Kingdom ranked third at 2.7%. Although ransomware activity remains heavily concentrated in North America, the top impacted countries span multiple continents, underscoring the global nature of this threat.
| Country | Ransomware Victims (out of total) |
| United States | 51% |
| Canada | 6% |
| United Kingdom | 2.7% |
| Germany | 2.5% |
| Brazil | 2.4% |
| Australia | 2.4% |
| Italy | 2.4% |
| France | 2.4% |
| India | 1.9% |
| Thailand | 1.8% |
Leading Ransomware Groups Maintain Strong Influence
Despite a fragmented ransomware ecosystem, a small number of groups continued to dominate activity in February. Qilin led global ransomware activity, responsible for 15% of published attacks, continuing its expansion following increased affiliate recruitment. Clop accounted for 13%, concluding a months‑long campaign exploiting Oracle E‑Business Suite zero‑day vulnerabilities. The Gentlemen, responsible for 11% of attacks, doubled its victim count compared to the previous month, reflecting rapid operational scaling. Notably, 49 different ransomware groups publicly impacted organizations worldwide during February, underscoring the breadth and resilience of the ransomware landscape.
- Qilin: One of the most established ransomware‑as‑a‑service (RaaS) groups, with a consistent track record of victim disclosures dating back to 2022. Originally operating under the name Agenda, the group rebranded as Qilin by September 2022, introducing a Rust‑based encryptor and expanding its RaaS infrastructure. Qilin provides affiliates with a full‑featured toolkit through a dedicated administrative panel, including an encryptor, negotiation infrastructure, and support services. Following RansomHub’s retirement, Qilin intensified its affiliate recruitment efforts and, since March 2025, has significantly increased the volume of victim listings on its data leak site (DLS).
- Clop: A ransomware group that, after a period of relative inactivity, has resumed publishing victims from a months‑long campaign dating back to at least August 2025. This activity represents the final stage of a large‑scale data‑theft and extortion operation exploiting two Oracle E‑Business Suite (EBS) zero‑day vulnerabilities, including the pre‑authentication RCE flaw CVE‑2025‑61882. This campaign aligns with Clop’s established strategy of targeting high‑value enterprise platforms to exfiltrate large datasets from numerous organizations across diverse global sectors.
- The Gentlemen: This ransomware group is a relatively new and technically sophisticated threat actor, first observed in 2025, conducting double‑extortion attacks by breaching networks, exfiltrating sensitive data, and encrypting systems to demand ransom payments. The group targets organizations across multiple sectors and operates a dedicated leak site to pressure victims into paying. Its ransomware is primarily written in Go and includes variants targeting Windows, Linux, and ESXi environments. Execution requires a password parameter, helping prevent accidental deployment and limiting exposure in analysis environments. The group also employs living‑off‑the‑land techniques, abusing legitimate system tools to move laterally, escalate privileges, and evade detection—demonstrating a controlled, operator‑driven, and mature intrusion capability.
What February’s Trends Reveal About the Evolving Threat Landscape
February 2026 confirms that cyber threats have entered a phase of sustained intensity rather than episodic spikes. While ransomware volumes temporarily rebalance, overall attack activity remains elevated, genAI‑driven exposure persists, and attackers continue to refine speed, precision, and scale. At Check Point Software, our research shows that reactive security models are no longer sufficient. Adversaries move faster, automate more effectively, and exploit vulnerabilities before traditional defenses can respond. A prevention‑first, multi‑layered security strategy—combining real‑time threat intelligence, AI‑powered prevention, and unified protection across cloud, network, endpoint, and users—is essential to reducing risk and building long‑term cyber resilience. Only by anticipating attackers’ next moves can organizations meaningfully stay ahead in today’s rapidly evolving threat landscape.



