
Iran-nexus Password Spray Campaign Targeting Cloud Environments, with a Focus on the Middle East
Key Findings
- Check Point Research (CPR) has been tracking an ongoing password-spraying campaign targeting Microsoft 365 environments across the Middle East, conducted by an Iran-linked threat actor. The campaign was carried out in three distinct waves of attacks, which took place on March 3, March 13, and March 23
- The campaign is primarily focused on Israel and the UAE, impacting more than 300 organizations in Israel and over 25 in the UAE. Activity associated with the same actor was also observed against a limited number of targets in Europe, the United States, the United Kingdom, and Saudi Arabia
- The activity primarily targeted municipalities, which play a critical role in responding to missile-related physical damage. Also, we observe some correlation between the targets of this campaign to cities that were targeted by missile attacks from Iran during March. This suggests the campaign was likely intended to support kinetic operations and Bombing Damage Assessment (BDA) efforts
Campaign Overview
Check Point Research identified a password-spraying campaign conducted by an Iran-nexus threat actor, targeting cloud environments of government entities, municipalities, energy-sector organizations, and private-sector companies amid the ongoing conflict in the Middle East, primarily in Israel and the UAE.
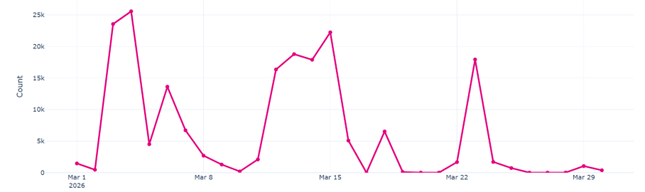
Figure 1 – Iran-nexus Password Spraying Volume Over Time – March 2026
Unlike common brute-force attacks, password spraying targets multiple accounts with the same set of weak or commonly used passwords. The technique is based on the assumption that at least one user will have weak credentials. In this campaign, the attackers used multiple source IP addresses to target numerous accounts, making detection based on atomic indicators such as IPs more difficult.

Figure 2 – Example organization A – Failed sign in attempts for accounts in the tenant
This technique is popular among advanced threat actors and has been used in the past by multiple advanced groups. Iran-nexus actors such as Peach Sandstorm and Gray Sandstorm are known to use this method for initial access and exfiltration.
The campaign targets multiple sectors, with Israel’s municipal sector appearing to be the primary focus, both in the number of organizations targeted and in the volume of password-spraying attempts per organization.

Figure 3 – Top targeted sectors
Attack Cycle
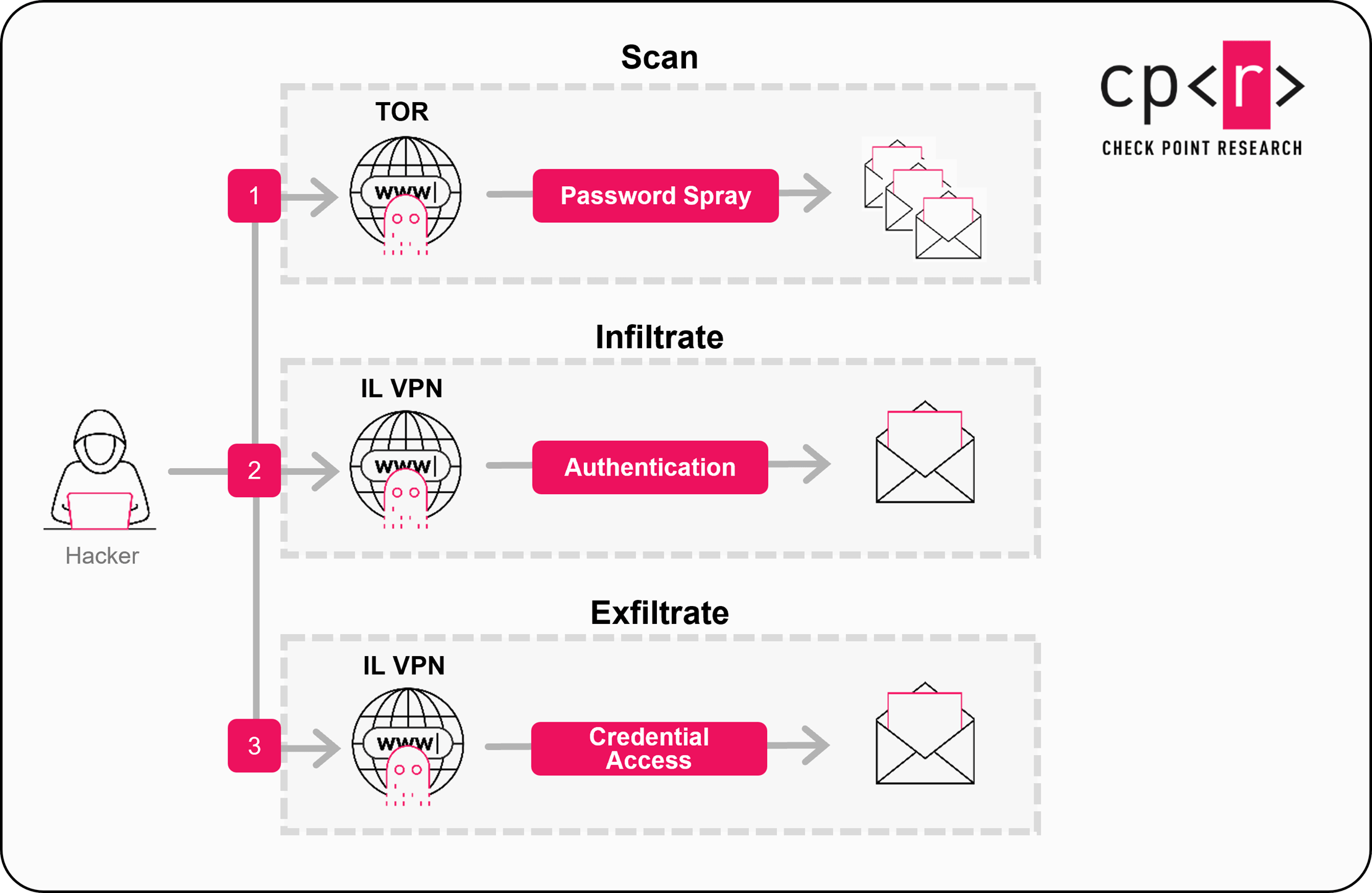
Figure 4 – Attack Cycle
- Scan: Intensive password-spraying against hundreds of organizations, mostly located in Israel and the United Arab Emirates. This scanning is conducted from Tor exit nodes, which are changed frequently to avoid blocking. The scan uses a User-Agent that masquerades as Internet Explorer 10 (IE10): Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; Trident/6.0)
- Infiltrate: This phase begins when the attacker finds valid credentials. The attacker then conducts the full login process from VPN IP addresses (Windscribe ip range 185.191.204.X or NordVPN ip range 169.150.227.X) Geolocated in Israel to evade Geo-restrictions
- Exfiltrate: Attacker leverages valid credentials to access sensitive data, such as personal email content
Attribution
Check Point Research assesses with moderate confidence that the actor behind the M365 password-spray activity originates from Iran. This assessment is based on the activity profile’s alignment with Iranian interests, including targeting of Israeli local government entities and organizations in the satellite, aviation, energy, and maritime sectors.
Analysis of M365 logs suggest similarities to Gray Sandstorm, including the use of red-team tools to conduct these attacks via Tor exit nodes. The threat actor used commercial VPN nodes hosted at AS35758 (Rachamim Aviel Twito), which aligns with recent activity tied to Iran-nexus operations in the Middle east.
Protection Recommendations:
1. Detect password spray anomalies
Monitor sign-in logs to identify password spray behavior patterns, specifically multiple authentication failures across many distinct user accounts originating from the same source IP
2. Restrict access using geo-fencing and TOR IP block controls
Apply conditional access controls to restrict authentication by approved geographic locations (geo-fencing) and to block high-risk anonymization networks, including TOR exit nodes
3. Enforce MFA tenant-wide and strengthen credential hygiene
Enforce multi-factor authentication (MFA) across the tenant for all users, with stricter controls for privileged/admin roles. Additionally, implement strong credential hygiene, including regular password updates where required by policy and risk posture.
4. Enable audit logs for post-compromise investigation
Ensure audit logging is enabled and retained appropriately to investigate post-authentication activity following any suspected successful password spray.
Check Point Email Security provides an additional level of protection against Microsoft 365 focused attacks.
IOCs
| Type | IOC |
| 185.191.204.202 | Windscribe VPN |
| 185.191.204.203 | Windscribe VPN |
| 169.150.227.3 | Nord VPN |
| 169.150.227.143 | Nord VPN |
| 169.150.227.146 | Nord VPN |



