
Tax Season 2026: How Cyber Criminals Are Preparing Their Attacks Months in Advance
Tax season remains one of the most attractive periods of the year for cyber criminals. As individuals and organizations exchange sensitive financial and identity data online, attackers take advantage of increased tax‑related activity to launch phishing campaigns, fraudulent websites, and malware attacks.
Check Point Research shows that these campaigns are not opportunistic. Threat actors begin preparing their infrastructure months in advance.
A Surge in Malicious Tax‑Related Domains
Between September 2025 and February 2026, hundreds of new domains containing tax‑related keywords or tax authority names were registered each month. This activity steadily increased toward the end of 2025 and intensified from November onward, indicating deliberate preparation ahead of tax‑season campaigns.
Notably, one in every 15 newly registered tax‑related domains has already been classified as malicious or suspicious, highlighting the widespread abuse of tax‑related themes.
In March 2026, both volume and risk increased further. The number of newly registered domains grew compared to earlier months in 2026, while the proportion of malicious and suspicious domains reached its highest level so far this year — one in every 10 new domains registered in March was flagged as risky.
IRS Impersonation Campaigns
Supporting this trend, Check Point Research identified multiple phishing domains impersonating the US Internal Revenue Service (IRS) in January 2026, including 2025irswebsiteislive[.]live and irstax-refund[.]xyz. These domains appear to be part of the same coordinated campaign, sharing nearly identical content and functionality.
The websites lure victims with fake “tax refund” offers, promising unusually high payouts such as weekly payments of $1,400 or a one‑time payment of $38,700. Victims are then prompted to submit sensitive personal information — including full name, Social Security number, phone number, and email address — followed by an identity verification process, strongly suggesting large‑scale data harvesting.
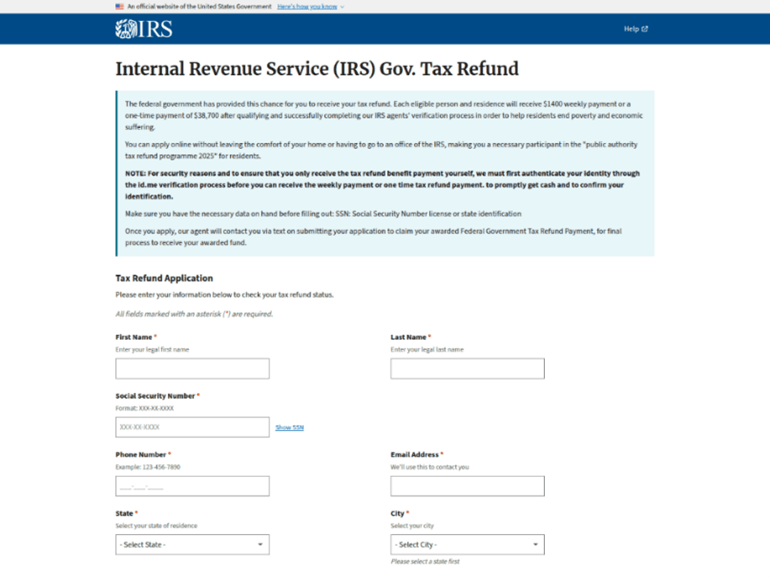
2025irswebsiteislive[.]live

irstax-refund[.]xyz
Malicious Tax Emails Targeting Spanish Organizations
Tax‑related attacks are not limited to fraudulent websites. In February 2026, Check Point Research identified a malicious email campaign impersonating the Spanish tax authority, Agencia Tributaria (AEAT).
In February 2026, an email was sent from a spoofed address [email protected], masquerading as a legitimate sender, to a Spanish industrial company, using the subject “AEAT – Notification Notice 2026” (translated from Spanish).
The email contained a malicious executable attachment (hash: bda5cc053c4d9eb09f6dd1c45892fb4c) classified as Trojan.Downloader / Trojan.Minix (NSIS) and operates as a loader, designed to download and execute additional malicious payloads.
Once executed, the malware enables the delivery of secondary threats, such as credential stealers or keyloggers, potentially leading to further compromise of the victim’s system and sensitive data.
| Date | 24-Feb-2026 |
| Sender | [email protected] |
| Subject | AEAT – Notification Notice 2026 (aeat – aviso de notificación 2026) |
| File Execution | 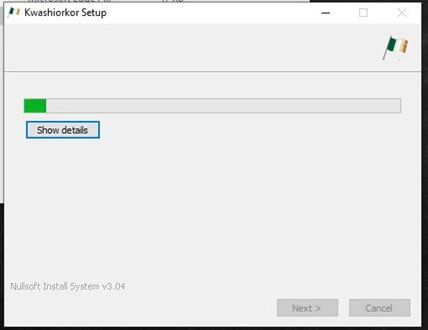 |
Staying Vigilant During Tax Season
Tax season creates ideal conditions for cyber crime: high volumes of sensitive data, expected official communications, and pressure to act quickly. As these findings show, cyber criminals continue to refine their tactics and expand their reach.
As tax deadlines approach, organizations and individuals should remain alert. Monitoring newly registered domains, identifying phishing attempts early, and preventing malicious files from executing are critical steps in reducing risk. Proactive security and informed users remain the strongest defense against tax‑related cyber threats.



