Malware Analysis – CTB-Locker
Executive Summary
CTB (Curve-Tor-Bitcoin) Locker is a crypto-ransomware variant. It is based on advanced algorithms which are used in different combinations, making CTB-Locker significantly more difficult to detect and neutralize.
CTB-Locker (aka Critroni or Onion) is based on a so-called encryptor, which encrypts all of a user’s personal data and extorts payment to decrypt the files. It is spread via email spam.
Kaspersky Lab recognizes CTB-Locker as a Trojan-Ransom.Win32.Onion. Distinctive features of this family include using combinations of cryptographic algorithms and features of the TOR network. The hackers extort payment in Bitcoins, known to provide anonymity in currency transactions.
In this report, we examine and analyze the traffic generated by CTB-Locker, and provide relevant statistics, protections and signatures developed by Check Point. Together with SenseCy, we also attribute the malware to Russian cyber-crime actors.
Overview
The goal of CTB-Locker (as its “CryptoLocker” counterpart) is to encrypt your files (those on your computer as well as on all your computer’s network shares) to extort a ransom in the form of 3 Bitcoins (value approximately $630).
The three elements used in this threat are:
1. Elliptic curve cryptography to perform the encryption.
2. TOR network features to ensure anonymity for the payment.
3. Bitcoin as the online currency used.
The most common infection method is via an email which looks like it was sent by an employee of the targeted company, and is directed at the management department. The email contains a fake invoice which is compressed in a “.zip” or “.cab” archive file. The archives contain a binary usually in a “.scr” file. Once opened, this file displays a decoy RTF document, waits five minutes, and then drops the actual CTB-Locker payload which performs the encryption routines.
Attribution
In a joint effort with SenseCy, CTB-Locker is attributed to “Tapkin”, who first posted it on a well-known Russian Underground Forum on June 10th 2014. Tapkin has demonstrated knowledge regarding CTB-Locker and its capabilities, as well as its technical components.
As far as we know, CTB-Locker was published only on Russian-speaking platforms and all discussions on the subject have been in the Russian language. Tapkin registered on three forums a few days before posting, does not have posts on other topics, and is not involved in other discussions. Tapkin stopped selling CTB-Locker on June 27th 2014, but offered it to only “serious” clients on November 19th 2014. Most recently, Tapkin posted CTB-Locker for sale on the Carding Forum on December 8th 2014. To date, Tapkin has remained active in the conversation and posts new updates of CTB-Locker.
Statistics
The chart below show the infected hosts over the past two weeks:
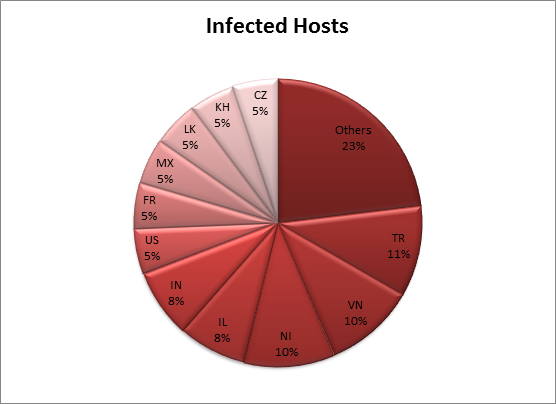
As we can see from the chart above, CTB-Locker does not discriminate its victims for a specific language or geo location and attacks all around the world.
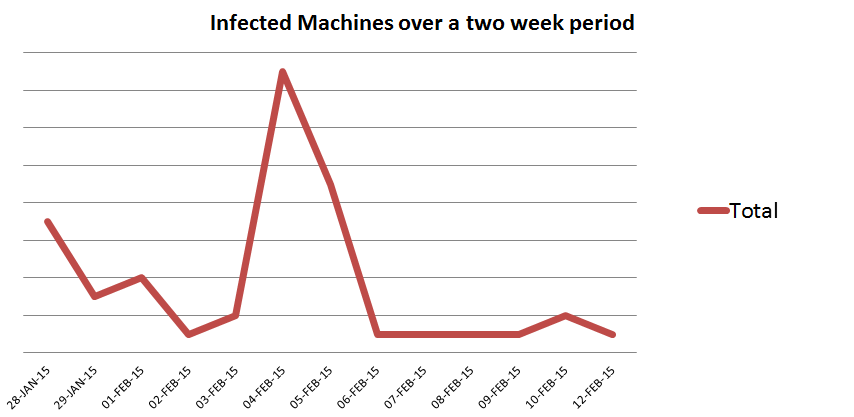
As we can see from the chart above, a spam campaign was probably initiated on February 4th, which caused the significant increase of infected gateways and hosts.
List of Relevant Signatures & Indicators
CTB-Locker can be detected on a victimized PC through network traffic analysis; Check Point customers are protected against CTB-Locker by a compilation of different Anti-Bot and Anti-Virus signatures of the format:
✓ Trojan-Ransom.Win32.CTB-Locker.<lowercase letter>
Related Hashes:
9fa13724e14c6acef19fdad6abc41b0c5e4a9c6328c003d2e79e1e3e5f5c253e
6e041641a168f66ece674f0cbf1c0ace77c9ce68e0900d374ddbebf7b2c449b9
6940031f8124e36d61a1d09688876b0e54cbfe5b431ded54a8936c6d21d51a5c
d0b3158d4cba466c1191db2f8c7de5386f1db7c545b20da8b7bb988d90cb37b2
5ce0a64b1fccee4cbaeec9fb2c1760dc3715f1cb28f34d66a710e2d31441de00
c31950bb15ec228fc2276ef501527ceb68b6e132376bff0f2b47bc2c98de1ab0
fb8159ae34d239ec17c6528c67b0c3ab1817385291e5228955a8d68b915a4b3b
4b747f699cdab219152094dd541ebcb6da7e47bbcc8fb33b226b0013d4c7d7f2
52e71ddec5f981cfd10f491102f155776b07ddef33ef8e2071a9b8857b87d930
c4d0a29c720aab28a3449331fc7d32e717371b9c1851e76d31bfb17bec882907
9bc837dd83af74ad920ade6b4ef4106eeb12683b901a167aabc6113e38251d54
Conclusion
CTB-Locker is a type of ransomware which is spread via email. When opened, the attached file drops a payload which performs encryption routines on all the computer’s files. Ransom in the form of Bitcoins is extorted from the user to decrypt the files. Network traffic analysis can detect CTB-Locker on an affected machine. The malware is with high certainty developed and distributed by and to Russian cyber-crime actors.
Appendix A – Technical Analysis
The infection procedure
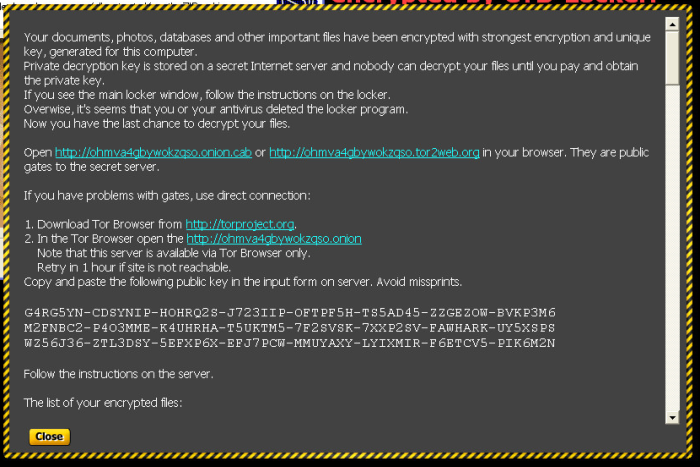
Within a few seconds of executing the sample, the screen displayed a warning that all the data was encrypted allowing 96 hours to transfer a payment to the attackers, or else it would be impossible to decrypt the files.
A list of encrypted files is provided:
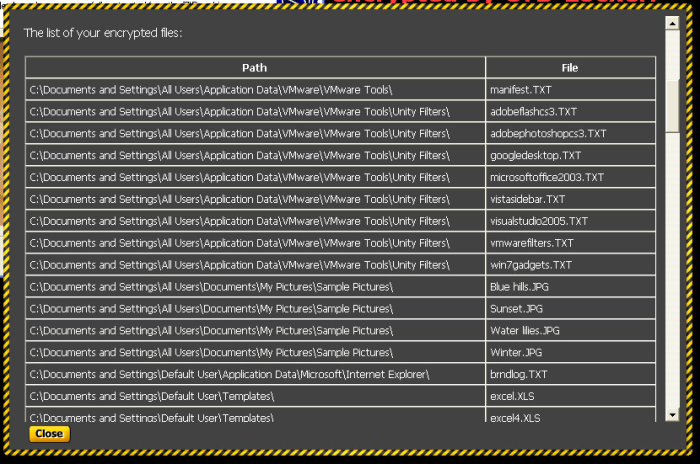
To demonstrate that the decryption was possible, five random files would be decrypted:

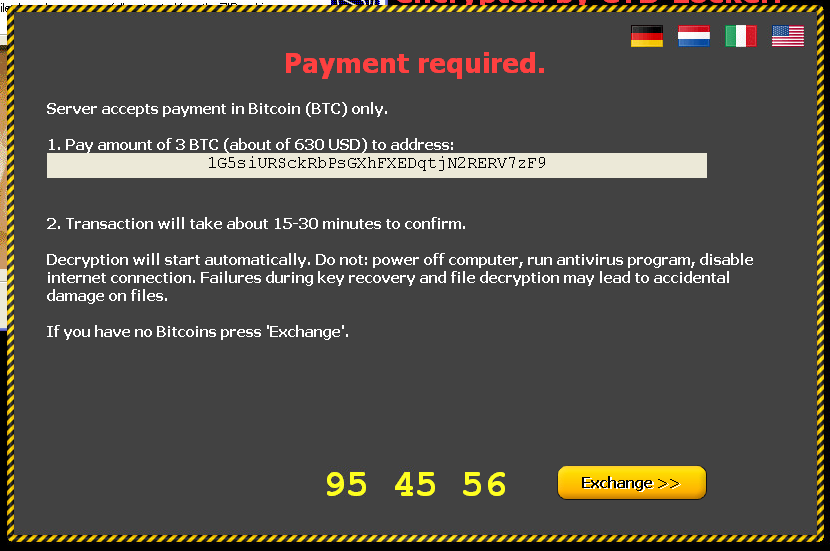
Finally, the CTB-Locker connects to a server to request a private key. After establishing a connection to the server, a message with instructions for payment is displayed. The “ransom” is 3 Bitcoins, which is the equivalent of $630. The payment address differs from message to message.
After delivering the payment message, CTB-Locker goes into standby mode, awaiting payment. Once payment is confirmed, it should connect to the server once more, obtain a key, and decrypt all data.
Note: On virtual machines with Windows XP, it took a long time and several attempts until a request to the server was accepted. On virtual machines with Windows 7, connection to the server occurred within a few seconds on the first try.
Network analysis
As mentioned previously, the CTB-Locker uses different encryption mechanisms; as a result, analyzing the traffic it generates is not a trivial task. Almost all data exchange is done through safe channels, and the packets contain no useful information. Nonetheless, we managed to find a few common packets.
After additional analysis of this Trojan on different virtual machines, we obtained six additional packet captures.
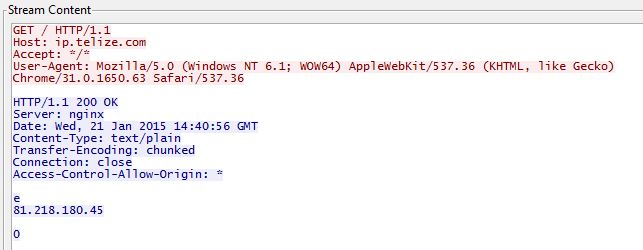
For example, at the beginning, CTB-Locker establishes a connection with ip.telize.com.
This service offers a REST API, which allows a visitor to get an IP address and to query location information from any IP address. It outputs JSON-encoded IP geolocation data.
This appears to be a legitimate query. However, the User-Agent has the same value in all packet captures with no regard to the OS on which it was created.
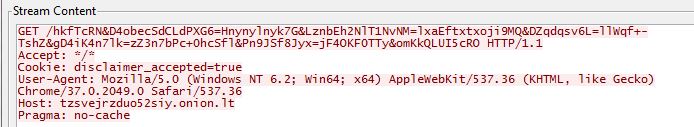
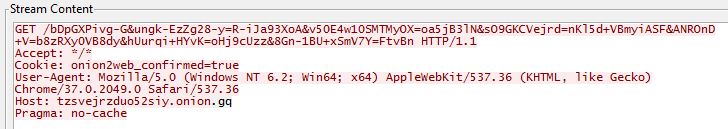
The next interesting GET-packets are:
Here we see the same User-Agent, a non-standard URL-query, and interesting cookie values.
Finally – A TCP packet starting with 17 03 with the length of more than 500 bytes was seen in all the network captures analyzed.