Getting your emails blocked? Don’t forget the semicolon;
Due to their common use in websites, JavaScript files are not detected by traditional Anti-Virus software. Scanning JavaScript files while browsing is virtually impossible due to its performance impact and probable high false positive rate, due to most sites using obfuscated JavaScript as a benign method to protect their intellectual property. To detect such attacks, the contextual data is needed.
If you let the Anti-Virus “know” that the source of the JavaScript is email based, it can overcome the mentioned limitation and block the JavaScript. This was the case with Gmail, which recently (in February) changed the allowed sent or received attachment policy to block JavaScript files.
We suspect this change came about due to the frequency of this attack vector and the difficulty of detecting malicious JavaScript. Gmail has access to Virus Total, another Alphabet Inc. company which scans files with multiple AV vendors. With evidence that scans are futile against malicious JavaScript, Google opted for increased security over usability.
Despite this policy change, we are still tracking many ongoing JavaScript scam campaigns through Check Point’s SandBlast detection. These ongoing campaigns suggest that many organizations’ email gateways do not completely block this vector.
Furthermore, we are seeing new attack methods which can get around this blocking method. One example is a CryptoLocker campaign which occurred simultaneously with Gmail’s announcement. In this case, the attackers sent an html file which persuaded users to download and click-open a JavaScript file that looked like an invoice, bypassing the Gmail restriction against JavaScript files in emails.
In the campaign, the user receives an email, titled ‘invoice’, in the regional language, which states the recipient has an invoice which needs to be printed.
Screenshot 1: ‘Invoice’ email received by a victim
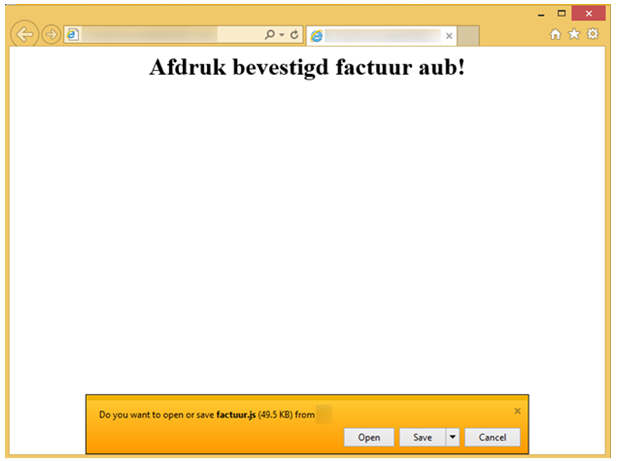
The attachment is an html file inside a zip. When the user unzips the file and opens the html file, the default browser downloads a new JavaScript file and opens a page enticing the user to open it.
Screenshot 2: A page asking the user to print the downloaded invoice.
If the user clicks on that “invoice” file to open and “print” it, what actually happens is that the JavaScript file is executed, which in turn downloads and executes CryptoLocker.
Other malicious actors have used this infection chain as well to spread malware, such as Pony and Zloader.
These events demonstrate the importance of technologies such as Check Point Threat Extraction that remove active content, as use of this attack technique is multiplying and might spread to other file types.