Social Engineering – Why mobile users are their own worst enemy
Social engineers have been using various devious methods to fool people for a long time. Social engineering, i.e the art of gaining access to buildings, systems or data by exploiting human psychology, rather than by breaking in or using technical hacking techniques, is almost as old as crime itself and has been used in many ways for decades.
In the online and mobile generations, social engineers try to fool unsuspecting users into clicking on malicious links and/or giving up sensitive information by pretending to be an acquaintance, trusted authorities or even just a recognisable app. By doing so, an attacker can manipulate users into disregarding their normal security precautions and can obtain access to secure information.
Attackers have an abundance of vectors with which to approach targets – whether by e-mail, social network, online advertisements or a single SMS.
Social Engineering – Mobile Security aspects:
Over the coming weeks, we’ll introduce you to the range of implications social engineering can have on mobile security both in enterprise and personal surroundings.
In this post, we survey the most common and in some ways, the most dangerous method, of social engineering in the mobile security domain – Malicious Advertising, or “Malvertising”.
Social Engineering – Mobile Malvertisements
Given the increasing usage of mobile devices both at home and at work, it’s hardly surprising that online ads now present the biggest malware threat to mobile users. In just over a year, Web ads have grown by 200% and have replaced pornography as the most prominent threat, with 20% of mobile ads directing users to malicious content.
The multiple points of entry into the advertising and marketing world make it difficult for the most experienced mobile device users to detect the difference between malicious and trustworthy ads. Trust and the human psyche are essential to the success of these attacks.
- Looking at ads, we differentiate between:
- “regular” ads. These are ads that appear,say, when you surf the Web using your mobile browser.
- ads the originate from “ad networks”. These are advertising frameworks that mobile developers embed into their applications in order to generate revenue (worth around $13 billion in 2013, the mobile ad market is projected to be worth more that $40 billion by 2017)
- Unlike ads displayed inside PC Web browsers, ads displayed within mobile apps are delivered by code this is actually part of those applications.
- While embedding the code for the ad or the advertising network into a mobile application ensures that ads get tracked and the developers get paid, this “foreign” code also represents a backdoor into the device.
- These additional codes run the cover the range from malicious ads that contain code capable of extracting sensitive information to advanced
mobile Remote Access Trojans (mRATs)
This access can be abused in several different ways:
- Collect sensitive user data such as apps installed on the device.
- Immediately install malware, for example, to steal credentials to sensitive apps
- Enable future installation of malware, aka a “time bomb”
- Refer the user to a rogue server for further downloading of malware
These are examples of malicious advertisements :
GG tracker:
Victims were shown an advertisement that directs them to a malicious website that resembles the Android Market installation screen.
The ad lured users into downloading one of the following apps that contained malware that, once downloaded, the malware registered the victim for premium subscription services:
- A porn app called “Sexy Girls”.
- A fake battery optimizing app named “t4t.power.management”.
JiFake:
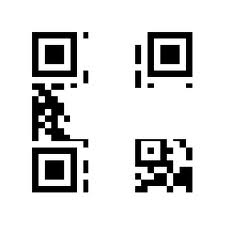
JiFake was the first recorded malicious use of a QR (quick response) code. As soon as the QR code had been scanned, it directed the victims to a URL containing the Jifake malware. Once installed, it signed the victims up to a premium-SMS service and began charging them fees without their knowledge.
Unlike a URL, which might raise suspicions if lacking https (SSL) or using an unknown domain – a malicious QR code looks exactly the same as a legitimate one. That, along with the fact that companies now print QR codes on buses, walls and soda cans – makes this an efficient method of propagating malware.
BadNews – Malicious Ad Networks
BadNews was one of the first instances of a malicious distribution network clearly posing as an ad network. Mainly targeting eastern European users, BadNews both signed victims up to Premium SMS services and had the ability to relay sensitive files and user data back to it’s Command and Control (C&C) server.
The creators of BadNews created a malicious advertising network as a way to get malicious bad code into Google Play. The ad network provided the attackers with a backdoor, through which they could push malware out to infected devices at a later date without having to worry about app scrutiny.
They also used the ad network to advertise less popular apps containing BadNews.
Research shows that BadNews was incorporated in 32 apps across four different developer accounts in Google Play. According to Google Play statistics, the combined affected applications have been downloaded between 2,000,000 – 9,000,000 times.
Social engineering has serious implications on many aspects of enterprise mobile security. Malicious ads are only the beginning. There are ways to fight these and many other threats – to keep your data safe.
To do so, it’s critical to be familiar with as many methods of attack as possible. Next week’s post will cover another aspect of social engineering – Fake Apps.