
Q1 2026 Ransomware Report: Fewer Groups, Higher Impact
Ransomware activity remained elevated in Q1 2026, continuing the trend established over the past year.
According to the State of Ransomware Q1 2026 report from Check Point Research, overall attack volume stayed near historic highs. At the same time, the structure of the ransomware ecosystem changed materially. After two years of increasing fragmentation, activity is consolidating around a smaller number of dominant groups. For organizations, this shift reduces the number of active actors but increases the potential impact of individual incidents.
Key Findings:
- 2,122 organizations were listed on ransomware data leak sites in Q1 2026, making it the second-highest Q1 on record
- The top 10 ransomware groups accounted for 71% of all victims, reversing the fragmented landscape seen throughout much of 2025
- Qilin remained the most active ransomware operation for the third consecutive quarter, posting 338 victims
- LockBit confirmed its comeback, posting 163 victims and re-entering the global top tier
Taken together, these figures show that ransomware volume has stabilized at a high baseline, while operational power is concentrating in fewer, more capable hands.
High Volume Is the New Normal
Check Point Research tracked more than 70 active ransomware data leak sites during Q1 2026. These sites recorded:
- More than 700 victims per month on average
- Minimal fluctuation between January, February, and March
At first glance, However, that comparison is misleading. Last year’s figures were inflated by a single mass-exploitation campaign. When that anomaly is removed, ransomware activity actually increased YoY.
The takeaway for business leaders is straightforward.
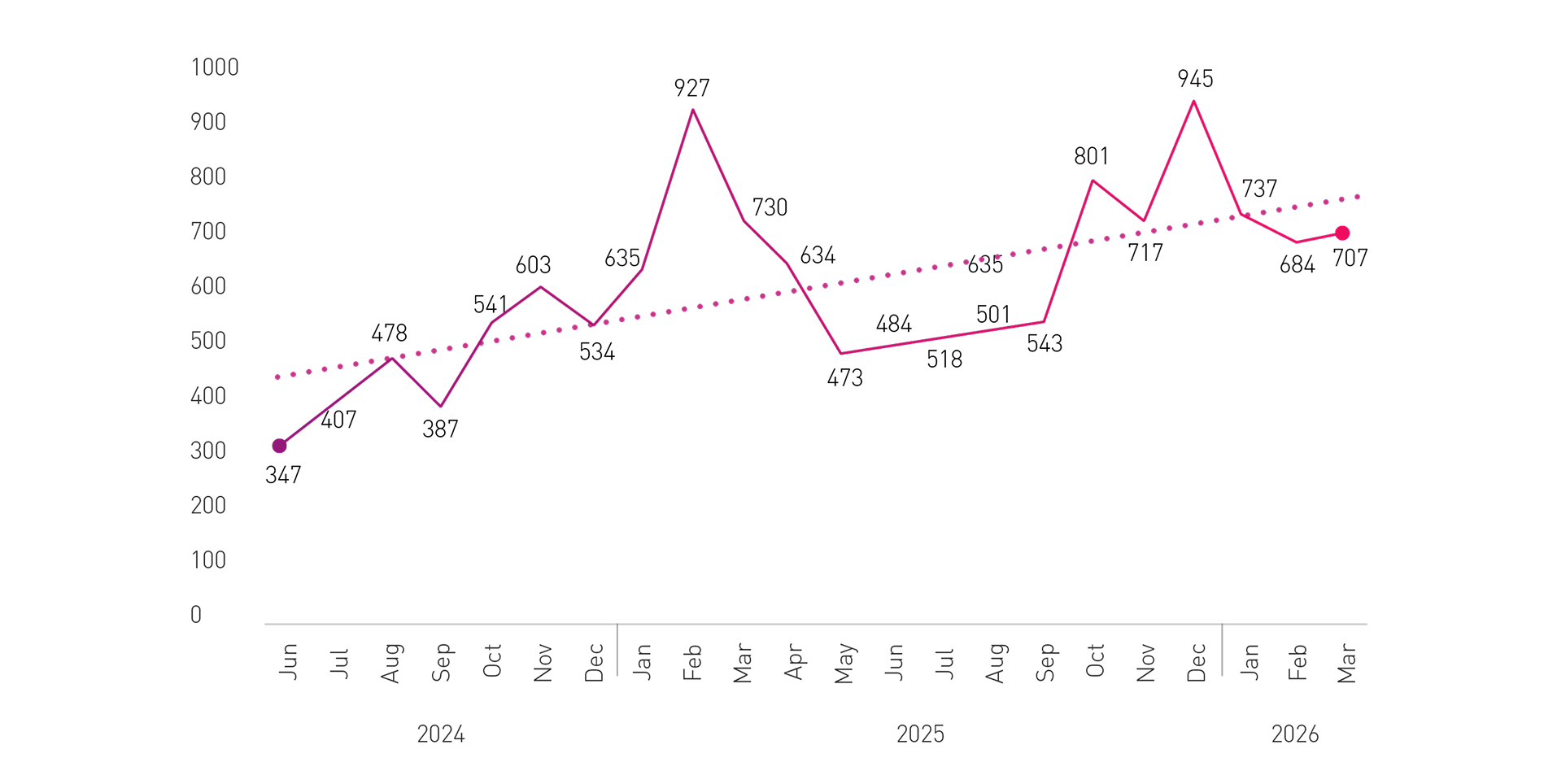
Figure 1 – Total number of reported ransomware victims in DLS, per month (Jun 2024 – Mar 2026)
From Fragmentation to Consolidation
The most important change this quarter is not how many attacks occurred, but who carried them out.
- In Q3 2025, ransomware activity was spread across a record number of groups
- By Q1 2026, the number of active groups had declined
- At the same time, the share of victims claimed by top operators surged past 70%
This pattern is familiar. Law enforcement pressure, infrastructure disruption, and the competitive landscape tend to scatter smaller players. Stronger groups survive, absorb displaced affiliates, and grow. In Q1 2026, groups such as Qilin, Akira, The Gentlemen, and LockBit together accounted for 41% of all victims, with the top 10 ransomware groups accounting for 71% of all victims.
For defenders, consolidation raises the stakes. Larger ransomware operations tend to be:
- More organized
- More operationally consistent
- More resilient to disruption
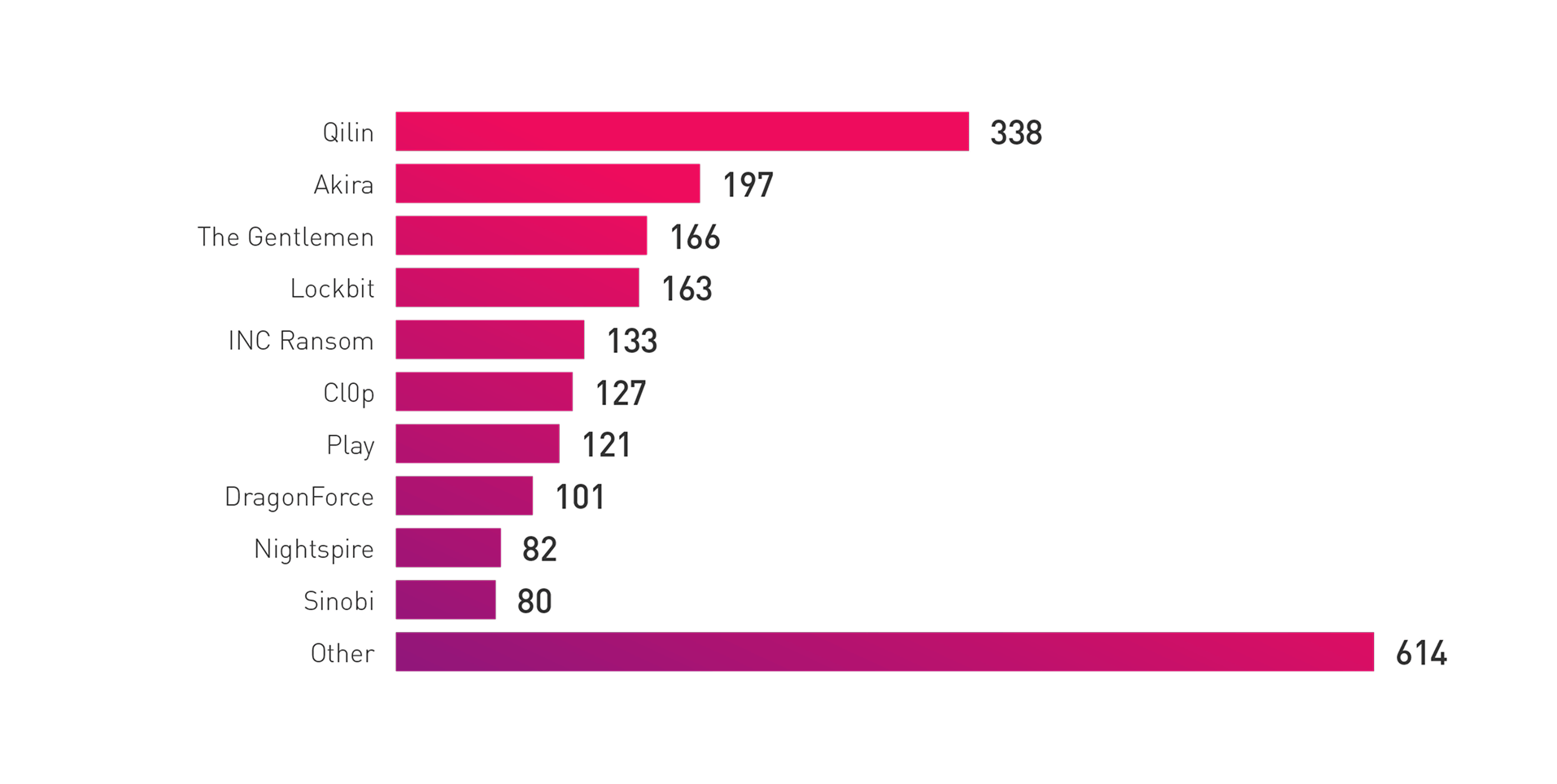
Figure 2 – Top 10 ransomware groups by number of publicly claimed victims – Q1 2026
The Breakout Story: The Gentlemen
One of the most notable increases in activity during Q1 2026 was attributed to The Gentlemen, a ransomware group that reached third place globally within a few months of initial activity.
Their growth was fueled by pre-positioned access at scale. Rather than relying on slow, opportunistic exploitation, the group operated with a large inventory, allowing it to launch attacks immediately and in volume.
Their targeting pattern also stands out:
- Only 13% of publicly extorted victims were based in the United States, compared to an ecosystem average of 49.6%
- Activity clustered in APAC and Latin America, mirroring the geographic distribution of compromised access points instead of a shift in the broader threat landscape
This disparity does not indicate deliberate avoidance of US targets, but rather reflects where the group already had established access. Increasingly in some cases, attackers go where access is available, not necessarily where victims are most lucrative.
LockBit’s Return, With a Strategic Shift
LockBit’s reappearance in Q1 2026 confirms that the group has recovered operationally after significant law enforcement disruption in 2024.
While overall activity more than doubled compared to the previous quarter, the most notable change was geographic. Historically focused on the United States, LockBit’s recent victims were spread more evenly across Europe, Latin America, and other regions.
The shift suggests a deliberate effort to reduce exposure to aggressive enforcement jurisdictions while maintaining scale. For global organizations, this reinforces a critical point. Geographic diversification by attackers expands risk, it does not reduce it.
Geographic and Industry distribution: How Access Shapes Impact
Ransomware activity in Q1 2026 shows that both industry and geographic impact are also shaped in some cases, by where attackers already have access.
Industries with high downtime sensitivity and complex environments continued to experience frequent attacks, including:
- Manufacturing
- Business services
- Healthcare
- Industrial sectors
The same access‑driven pattern was visible geographically:
- The United States accounted for nearly half of all reported victims (49.6%), consistent with its large enterprise footprint, with Western developed economies making up the clear majority of targets.
- Thailand accounted for 10.8% of victims tied to a single dominant ransomware group (The Gentlemen), pushing it into the top‑targeted countries for the first time,
- Play concentrated 85.1% of its activity on US‑based organizations, demonstrating how individual groups can heavily focus on a certain country
Taken together, these trends show that ransomware risk is less about sector or location in isolation, and more about the underlying exposure created by deployed technology, connectivity, and available access paths.
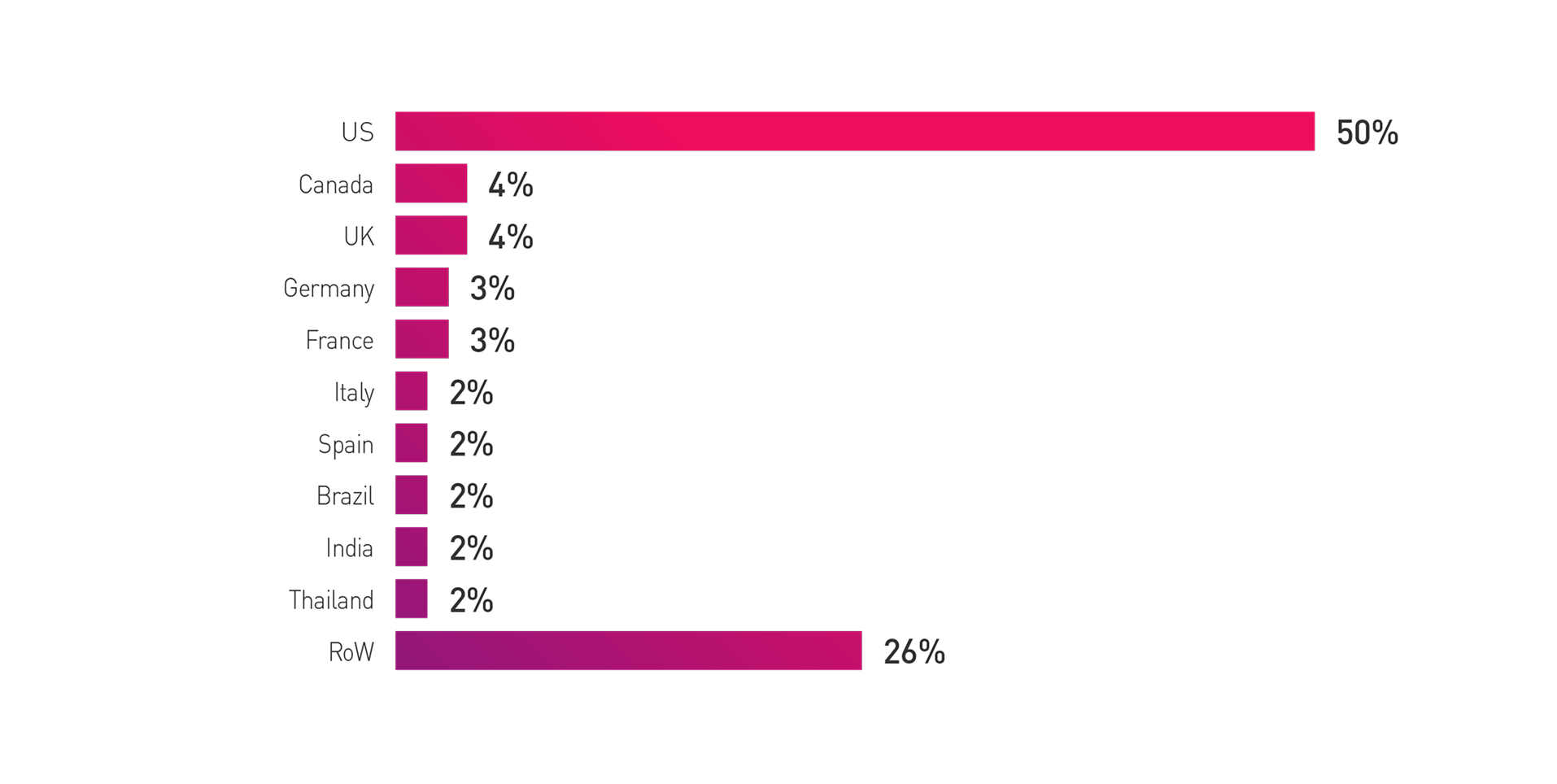
Figure 03 – Reported ransomware victims, by country
What This Means for Organizations
Ransomware in 2026 is defined by concentration, not volume. Fewer groups now drive the majority of attacks, and these operators are more capable, better resourced, and harder to disrupt.
For organizations, this changes the risk equation:
- Fewer incidents may occur, but each carries greater potential impact
- Attacks are more repeatable and access‑driven
- Prevention and containment matter more than reaction alone
In practical terms, defense means:
Stopping Ransomware at the Network and Cloud Access Layer
Ransomware and extortion attacks often enter through exposed infrastructure, cloud services, or remote access paths. This is addressed through Hybrid Mesh Network Security, by applying consistent, AI‑driven threat prevention across networks, clouds, data centers, and remote users.
Capabilities such as network firewalls, SASE Internet Access, and CASB block malicious downloads, phishing, exploits, and ransomware before they reach devices. If an infection occurs, Zero Trust controls in SASE Private Access limits ransomware impact by restricting attackers to only the data a compromised user can access.
Reducing Ransomware Exposure Before Exploitation
As ransomware attacks become faster and more targeted, reducing exposure before exploitation is critical. This is the focus of the Exposure Management pillar, which helps organizations identify which assets, vulnerabilities, misconfigurations, and access paths attackers can realistically exploit.
By correlating live ransomware intelligence with internal exposure and validating safe remediation paths, security teams can close the most likely attack vectors early and reduce the likelihood of business disruption.
Protecting Users as a Primary Entry Point
Many ransomware attacks still begin with user interaction, such as phishing emails, malicious links, or compromised credentials. Workspace Security addresses this risk by protecting users across email, browsers, SaaS applications, and endpoints.
Using AI‑driven detection and global threat intelligence, Workspace Security blocks delivery vectors, prevents credential abuse, and disrupts command‑and‑control activity, helping organizations contain ransomware before it spreads or encrypts critical systems.
Join our upcoming webinar to hear directly from Check Point Research as we review the key findings from the Q1 2026 Ransomware Report and discuss what these trends mean for organizations and defenders today. Register for the webinar or download the Q1 report.



