
Unzipping the Threat: How to Block Malware Hidden in Password-Protected ZIP Files
As malware evades detection by hiding inside password-protect zip files, new Threat Emulation capabilities enable inspecting and blocking malicious ZIP files without requiring their password.
As cyber defenses evolve, so do attacker tactics. One of the most persistent evasion techniques in the wild involves embedding malware inside password-protected ZIP files, making it difficult for traditional security tools to inspect their content.
The Challenge: Breaking the Password Delivery Chain
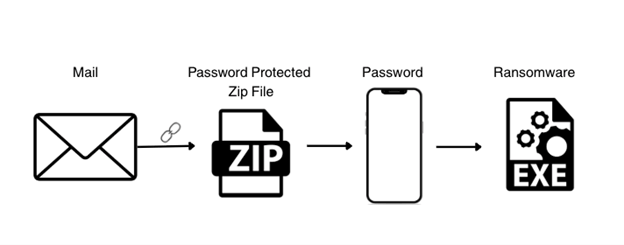
Attackers have adapted. Their new strategy? Splitting the delivery path:
- The malicious ZIP file is sent via email.
- The password arrives through an out-of-band channel, often SMS or messaging apps.
This multi-channel approach is designed to bypass conventional security controls, making it harder for systems to correlate the file and its password, and therefore harder to detect the threat.
The Breakthrough: Password-less Prevention
To block malicious password-protected archives without requiring their password, organizations are now protected with the new Encrypted Archive Engine. This innovation leverages ThreatCloud AI’s extensive malware intelligence databases, analyzing historical patterns and characteristics to detect newly emerging threats at the moment they’re deployed, regardless of password complexity.
How It Works
Our approach examines:
- Structural patterns within encrypted archives
- Metadata characteristics that correlate with malicious intent
- Delivery context and associated behavioral indicators
- Historical malware signatures adapted for encrypted content analysis
This method has already proven its effectiveness, preventing the delivery and download of thousands of malicious files and protecting enterprises from previously undetectable threats.
Real-World Impact: Case Study
Anubis Ransomware Detected in Customer Environment via Harmony Endpoint
Customer Profile: Information technology company
Platform: Harmony Endpoint
Detection Date: August 2025
Threat Classification: Critical – Anubis Ransomware Family
The ransomware campaign started with a targeted phishing email containing a password-protected ZIP folder. The password was provided through an out-of-band channel. Then, by using social engineering, the perpetrators tried to convince the victim to extract and execute the malicious payload.
The malicious executable, from the Anubis ransomware family, is protected using strong cryptographic algorithms, and usually targets backup systems (e.g., VEEAM, Acronis), databases servers (e.g., SQL) and cloud storage synchronization folders.
Outcome: The new engine successfully blocked the malicious ZIP file during the initial download delivery phase, before the victim had the chance to open the key.
Key Success Factors:
- Password-Independent Analysis: Detection occurred without needing to decrypt the ZIP archive.
- Proactive Prevention: Threat neutralized at the perimeter before reaching the endpoint.
- Zero Data Loss: No file encryption or data exfiltration occurred.
The Bigger Picture: Why This Matters
The Anubis ransomware case demonstrates the critical importance of password-independent detection in modern threat prevention.
The Encrypted Archive Engine leverages ThreatCloud AI to recognize malicious patterns and can prevent the delivery and download of new malware variants based on behavioral and structural analysis.
As adversaries continue to innovate their evasion techniques, Check Point remains committed to detect never-before-seen zero-day threats to protect its customers. This new engine represents a paradigm shift in protecting against advanced delivery mechanisms and is just one example of how we stay a step ahead to deliver the most effective security across the hybrid mesh network in clouds, networks, and edge environments
See how we topped the chart in the NSS Labs Enterprise Firewall Comparative Report.



